Why choose Lead4Pass CAS-004 dumps?
Not all certification dump platforms can help you pass the exam 100%. Lead4Pass, Pass4sure, Pass4itusre, and Examtopics are all established certification dumps platforms. They definitely stand among the best dumps platforms! I just want to tell the novice students the real situation here! Many experienced certification students know it. My topic today is CAS-004 dumps, and I will not introduce all dumps platforms one by one. But I want to tell you that the most cost-effective is Lead4pass. You can access these platforms, and I’m talking about the real situation.
There are still many new platforms appearing in front of everyone, I will not comment on them, but I can tell you that the most authoritative old websites are the above websites.
How to pass the CAS-004 exam?
Lead4Pass CAS-004 dumps https://www.leads4pass.com/cas-004.html(PDF +VCE). For both PDF and VCE learning modes. You can use either or both of these to help you learn the latest and most effective exam questions, which help You successfully pass the exam.
What is the difference between CAS-003 and CAS-004?
CAS-003 Published: April 2, 2018
Exam Description: CASP+ covers the technical knowledge and skills required to conceptualize, engineer, integrate and implement secure solutions across complex environments to support a resilient enterprise.
Retirement: April 5, 2022
CAS-004 Published: October 6, 2021
Exam Description: CASP+ covers the technical knowledge and skills required to architect, engineer, integrate, and implement secure solutions across complex environments to support a resilient enterprise while considering the impact of governance, risk, and compliance requirements.
Before you get a full CAS-004 dumps, you can also experience a small test in advance. I will share 12 CAS-004 test questions for free to help you test online, and the answers will be announced at the end of the test.
Download the latest CompTIA CAS-004 dumps PDF for free:
https://drive.google.com/file/d/1cUO2SOU1tH5fidaQSGQssHOIW3la0dfW/
https://drive.google.com/file/d/1IbvnTbTz7x2VbxDQ1GHCSEII5xMN55Pn/
https://drive.google.com/file/d/1gPzIc5NxyzqTe5jbFzvmofpUGr5d4CUr/
https://drive.google.com/file/d/1HTuRmBFIxx6IdcHgWxydtzAE7QEHNsVX/
Latest CAS-004 dumps Exam Questions and Answers Read Online
| Number of exam questions | Exam name | From | Release time | Last updated |
| 15 | CompTIA Advanced Security Practitioner (CASP+) | Lead4Pass | Dec 05, 2022 | CAS-004 dumps |
New Question 1:
Which of the following are risks associated with vendor lock-in? (Choose two.)
A. The client can seamlessly move data.
B. The vendor can change product offerings.
C. The client receives a sufficient level of service.
D. The client experiences decreased quality of service.
E. The client can leverage a multi-cloud approach.
F. The client experiences increased interoperability.
Correct Answer: BD
New Question 2:
A security analyst is concerned that a malicious piece of code was downloaded on a Linux system. After some research, the analyst determines that the suspected piece of code is performing a lot of input/output (I/O) on the disk drive.
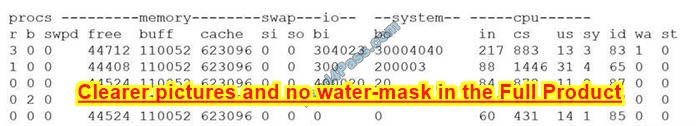
Based on the output above, from which of the following process IDs can the analyst begin an investigation?
A. 65
B. 77
C. 83
D. 87
Correct Answer: C
New Question 3:
SIMULATION
An administrator wants to install a patch to an application.
INSTRUCTIONS
Given the scenario, download, verify, and install the patch in the most secure manner.
The last installation that is completed will be the final submission.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.

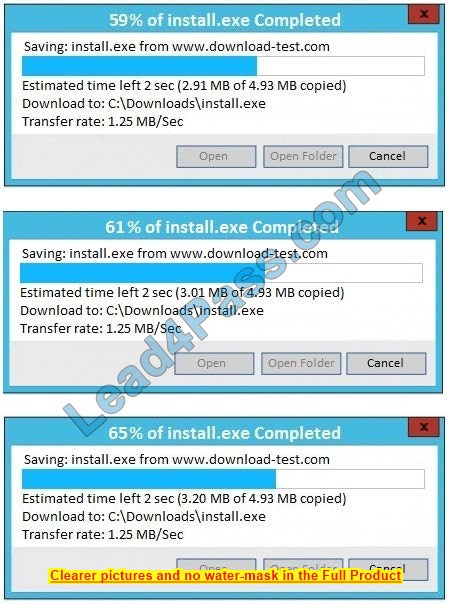
Correct Answer: See the below.
In this case, the second link should be used (This may vary in the actual exam). The first link showed the following error so it should not be used.
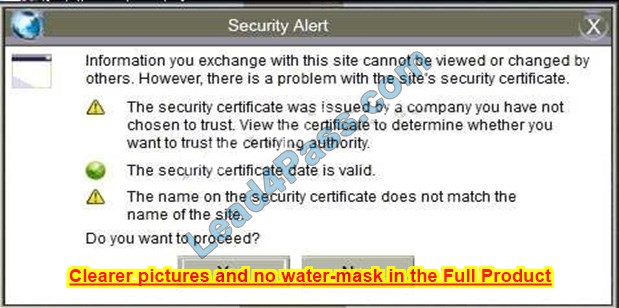
Also, Two of the link choices used HTTP and not HTTPS as shown when hovering over the links as shown:

Since we need to do this in the most secure manner possible, they should not be used.
Finally, the second link was used and the MD5 utility of MD5sum should be used on the install.exe file as shown. Make sure that the hash matches.
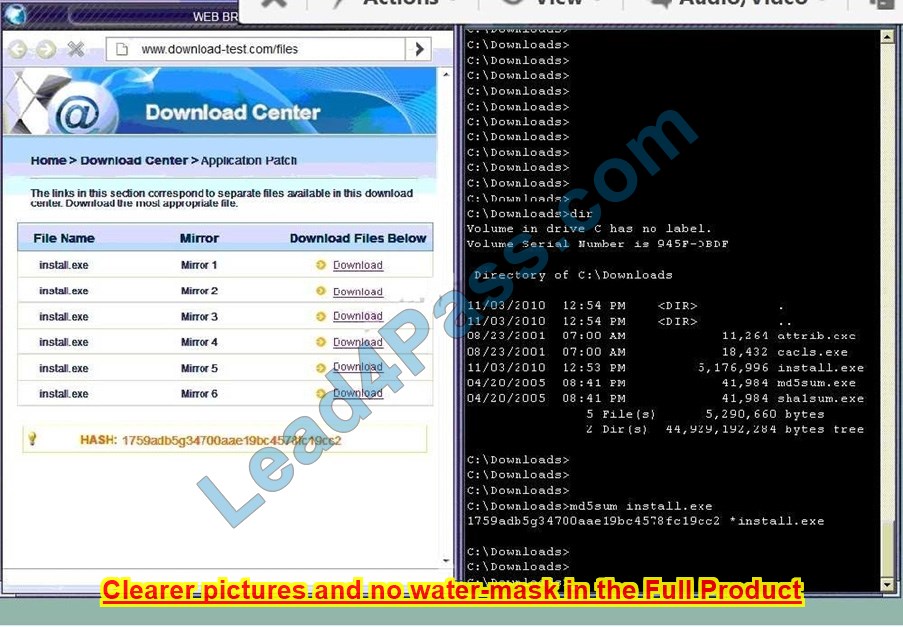
Finally, type in install.exe to install it and make sure there are no signature verification errors.
New Question 4:
A security engineer thinks the development team has been hard-coding sensitive environment variables in its code. Which of the following would BEST secure the company\’s CI/CD pipeline?
A. Utilizing a trusted secrets manager
B. Performing DAST on a weekly basis
C. Introducing the use of container orchestration
D. Deploying instance tagging
Correct Answer: A
Reference: https://about.gitlab.com/blog/2021/04/09/demystifying-ci-cd-variables/
New Question 5:
An enterprise is deploying APIs that utilize a private key and a public key to ensure the connection string is protected. To connect to the API, customers must use the private key. Which of the following would BEST secure the REST API connection to the database while preventing the use of a hard-coded string in the request string?
A. Implement a VPN for all APIs.
B. Sign the key with DSA.
C. Deploy MFA for the service accounts.
D. Utilize HMAC for the keys.
Correct Answer: B
Reference: https://eclipsesource.com/blogs/2016/07/06/keyed-hash-message-authentication-code-in-rest-apis/
New Question 6:
A company runs a well-tended, on-premises fitness club for its employees, about 200 of them each day. Employees want to sync the center\’s login and attendance program with their smartphones. Human resources, which manages the contract for the fitness center, has asked the security architecture to help draft security and privacy requirements.
Which of the following would BEST address these privacy concerns?
A. Use biometric authentication.
B. Utilize geolocation/geofencing.
C. Block unauthorized domain bridging.
D. Implement containerization
Correct Answer: A
New Question 7:
A systems administrator is preparing to run a vulnerability scan on a set of information systems in the organization. The systems administrator wants to ensure that the targeted systems produce accurate information, especially regarding configuration settings.
Which of the following scan types will provide the systems administrator with the MOST accurate information?
A. A passive, credentialed scan
B. A passive, non-credentialed scan
C. An active, non-credentialed scan
D. An active, credentialed scan
Correct Answer: D
New Question 8:
Company A has noticed abnormal behavior targeting their SQL server on the network from a rogue IP address. The company uses the following internal IP address ranges: 192.10.1.0/24 for the corporate site and 192.10.2.0/24 for the remote
site. The Telco router interface uses the 192.10.5.0/30 IP range.
Instructions: Click on the simulation button to refer to the Network Diagram for Company A.
Click on Router 1, Router 2, and the Firewall to evaluate and configure each device.
Task 1: Display and examine the logs and status of Router 1, Router 2, and Firewall interfaces.
Task 2: Reconfigure the appropriate devices to prevent the attacks from continuing to target the SQL server and other servers on the corporate network.
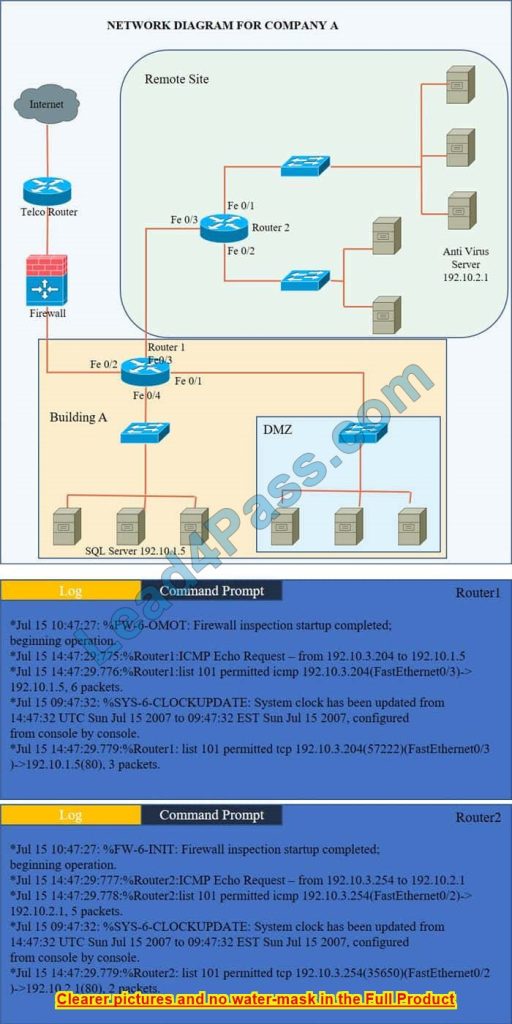
Hot Area:

Correct Answer:

We have the traffic coming from two rogue IP addresses: 192.10.3.204 and 192.10.3.254 (both in the 192.10.30.0/24 subnet) going to IPs in the corporate site subnet (192.10.1.0/24) and the remote site subnet (192.10.2.0/24). We need to Deny (block) this traffic at the firewall by ticking the following two checkboxes:

New Question 9:
A healthcare system recently suffered from a ransomware incident As a result the board of directors decided to hire a security consultant to improve existing network security. The security consultant found that the healthcare network was completely flat, had no privileged access limits and had open RDP access to servers with personal health information. As the consultant builds the remediation plan, which of the following solutions would BEST solve these challenges? (Select THREE).
A. SD-WAN
B. PAM
C. Remote access VPN
D. MFA
E. Network segmentation
F. BGP
G. NAC
Correct Answer: ACE
New Question 10:
A company is preparing to deploy a global service.
Which of the following must the company do to ensure GDPR compliance? (Choose two.)
A. Inform users regarding what data is stored.
B. Provide opt-in/out for marketing messages.
C. Provide data deletion capabilities.
D. Provide optional data encryption.
E. Grant data access to third parties.
F. Provide alternative authentication techniques.
Correct Answer: AC
The main rights for individuals under the GDPR are to:
1.
allow subject access
2.
have inaccuracies corrected
3.
have information erased
4.
prevent direct marketing
5.
prevent automated decision-making and profiling
6.
allow data portability (as per the paragraph above) https://www.clouddirect.net/11-things-you-must-do-now-for-gdpr-compliance/
New Question 11:
A networking team was asked to provide secure remote access to all company employees. The team decided to use a client-to-site VPN as a solution. During a discussion, the Chief Information Security Officer raised a security concern and asked the networking team to route the Internet traffic of remote users through the main office infrastructure. Doing this would prevent remote users from accessing the Internet through their local networks while connected to the VPN.
Which of the following solutions does this describe?
A. Full tunneling
B. Asymmetric routing
C. SSH tunneling
D. Split tunneling
Correct Answer: B
New Question 12:
Ransomware encrypted the entire human resources files are for a large financial institution. Security operations personnel were unaware of the activity until it was too late to stop it. The restoration will take approximately four hours, and the last backup occurred 48 hours ago. The management team has indicated that the RPO for a disaster recovery event for this data classification is 24 hours.
Based on RPO requirements, which of the following recommendations should the management team make?
A. Leave the current backup schedule intact and pay the ransom to decrypt the data.
B. Leave the current backup schedule intact and make the human resources files read-only.
C. Increase the frequency of backups and create SIEM alerts for IOCs.
D. Decrease the frequency of backups and pay the ransom to decrypt the data.
Correct Answer: C
New Question 13:
A company\’s internet connection is commonly saturated during business hours, affecting internet availability. The company requires all Internet traffic to be business related After analyzing the traffic over a period of a few hours, the security administrator observes the following:
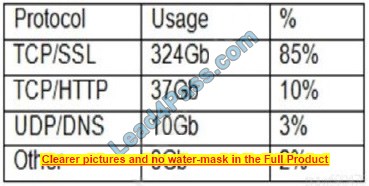
The majority of the IP addresses associated with the TCP/SSL traffic resolve to CDNs
Which of the following should the administrator recommend for the CDN traffic to meet the corporate security requirements?
A. Block outbound SSL traffic to prevent data exfiltration.
B. Confirm the use of the CDN by monitoring NetFlow data.
C. Further investigate the traffic using a sanctioned MITM proxy.
D. Implement an IPS to drop packets associated with the CDN.
Correct Answer: A
New Question 14:
In preparation for the holiday season, a company redesigned the system that manages retail sales and moved it to a cloud service provider. The new infrastructure did not meet the company\’s availability requirements. During a postmortem analysis, the following issues were highlighted:
1.
International users reported latency when images on the web page were initially loading.
2.
During times of report processing, users reported issues with inventory when attempting to place orders.
3.
Despite the fact that ten new API servers were added, the load across servers was heavy at peak times.
Which of the following infrastructure design changes would be BEST for the organization to implement to avoid these issues in the future?
A. Serve static content via distributed CDNs, create a read replica of the central database and pull reports from there, and auto-scale API servers based on performance.
B. Increase the bandwidth for the server that delivers images, use a CDN, change the database to a non-relational database, and split the ten API servers across two load balancers.
C. Serve images from an object storage bucket with infrequent read times, replicate the database across different regions and dynamically create API servers based on load.
D. Serve static-content object storage across different regions, increase the instance size on the managed relational database, and distribute the ten API servers across multiple regions.
Correct Answer: A
New Question 15:
A penetration tester obtained root access on a Windows server and, according to the rules of engagement, is permitted to perform post-exploitation for persistence. Which of the following techniques would BEST support this?
A. Configuring system services to run automatically at startup
B. Creating a backdoor
C. Exploiting an arbitrary code execution exploit
D. Moving laterally to a more authoritative server/service
Correct Answer: B
…
Complete CAS-004 Dumps Latest Update Dec 2022:https://www.leads4pass.com/cas-004.html (Total Questions: 325 Q&A). Participate in the full exam program and pass the exam 100% successfully
By the way, check out more free CAS-004 dump PDFs:
https://drive.google.com/file/d/1cUO2SOU1tH5fidaQSGQssHOIW3la0dfW/
https://drive.google.com/file/d/1HTuRmBFIxx6IdcHgWxydtzAE7QEHNsVX/
https://drive.google.com/file/d/1gPzIc5NxyzqTe5jbFzvmofpUGr5d4CUr/
https://drive.google.com/file/d/1IbvnTbTz7x2VbxDQ1GHCSEII5xMN55Pn/