I passed CompTIA Cloud+ CV0-004 in March 2026 with a score around 780. Not amazing, not terrible — just enough to get through. I studied for about 10 days while working full-time as a cloud operations engineer, somewhere between firefighting AWS issues and pretending I fully understood Azure networking quirks.
Here’s the thing: if you’re expecting a clean, structured “study guide,” this isn’t it. This is more like what actually happened — the confusion, the wrong assumptions, the “wait… what is this question even asking?” moments.
And honestly? That’s exactly what this exam tests.
What Actually Changed in 2026 (Not What You Think)
The Exam Feels More “Real” Than Before
On paper, the CV0-004 exam hasn’t changed dramatically — still about 90 questions in 90 minutes, with a passing score of 750 . Same domains: architecture, deployment, security, operations, DevOps, troubleshooting.
But the behavior of the exam feels completely different.
What surprised me was how little it cared about textbook definitions. Instead, it throws you into messy, half-broken environments and basically asks:
“What would you actually do here?”
This is where most guides are misleading. They still treat Cloud+ like a knowledge exam. It’s not.
DevOps and Multi-Cloud Are Not Optional Anymore
You can’t ignore things like Infrastructure as Code, containerization, or CI/CD pipelines anymore. These are core, not optional extras .
I initially got this wrong because I assumed “vendor-neutral” meant “surface-level.” It doesn’t.
Instead, it expects you to understand:
- Why Terraform might fail in a deployment
- What happens when a Kubernetes pod can’t reach a service
- How a misconfigured IAM policy breaks automation
And it won’t explicitly say it. You have to infer it.
The Biggest Difficulty Nobody Talks About
Ambiguity in Questions
This exam is weirdly vague. Not poorly written — just intentionally unclear.
You’ll see questions like:
- A log snippet with partial errors
- A diagram with missing context
- A scenario where multiple answers seem correct
And you’re supposed to pick the best one.
That’s not easy.
Strong Opinion:
Most CV0-004 guides are outdated because they train you to recognize answers — not evaluate them.
Time Pressure + PBQs Combo
You get performance-based questions (PBQs), and they’re not trivial. Things like:
- Troubleshooting connectivity between subnets
- Identifying misconfigured storage or compute resources
- Interpreting monitoring dashboards
These eat time fast.
And since the exam is only 90 minutes total , you can’t afford to get stuck.
My 10-Day Preparation Story (Messy but Real)
Days 1–3: Overconfidence Phase
I thought, “I’ve been working with AWS and Azure for years… how hard can this be?”
Big mistake.
I skimmed through some materials, did a few practice questions, and felt comfortable.
Too comfortable.
Days 4–7: Confusion + Course Correction
This is where things started falling apart.
Practice questions felt easy… but when I tried scenario-based ones, I kept second-guessing myself.
I remember one question about log analysis — I picked the technically correct answer, but it wasn’t the operationally practical one.
That’s when it clicked:
This exam is about decision-making under uncertainty.
Days 8–10: Simulation Mindset Shift
I stopped “studying” and started thinking like I was on-call.
Instead of asking:
- “What is the right answer?”
I started asking:
- “What would I do if this broke in production?”
That shift made all the difference.
What Actually Works (Practical Strategy)
Think Like an Operator, Not a Student
Forget memorization.
Focus on:
- How systems fail
- What logs actually look like
- What breaks first in real environments
Because that’s what the exam tests.
Strong Opinion:
This exam is not about memorization — it’s about decision-making under uncertainty.
Logs, Metrics, and Troubleshooting First
If I had to redo it, I’d start here:
- Log analysis
- Monitoring tools
- Network troubleshooting
Not architecture. Not theory.
Because nearly every question ties back to:
- “Something is broken — now what?”
Resources I Used (Including Leads4Pass)
I didn’t use anything fancy, but I mixed a few things:
- Some online courses (honestly, too generic)
- Some Practice exams (useful, but limited)
- Leads4Pass — surprisingly helpful for exposing weak spots
- Random lab scenarios I created myself
Here’s the truth:
No single resource is enough.
Strong Opinion:
The biggest problem with Cloud+ prep is not difficulty — it’s fragmentation.
You have to stitch everything together yourself.
Is Cloud+ CV0-004 Worth It in 2026?
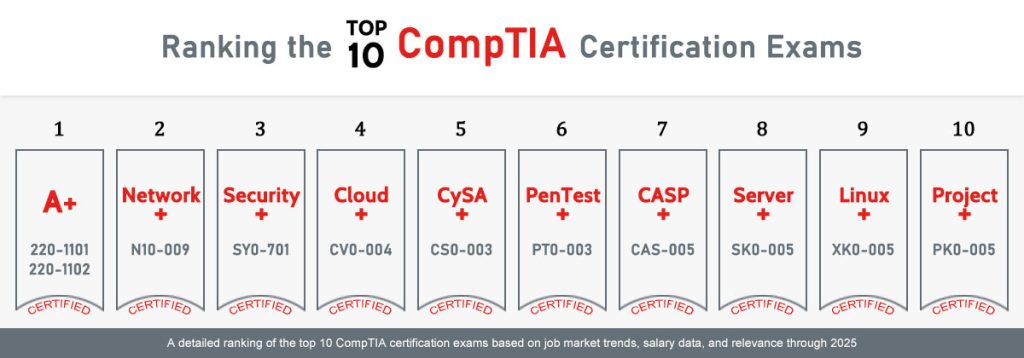
Compared to Other CompTIA Certs
Cloud+ sits in a weird place.
Compared to:
- Security+ → more theoretical
- CySA+ → more security-focused
- PenTest+ → offensive
- Linux+ → system-level
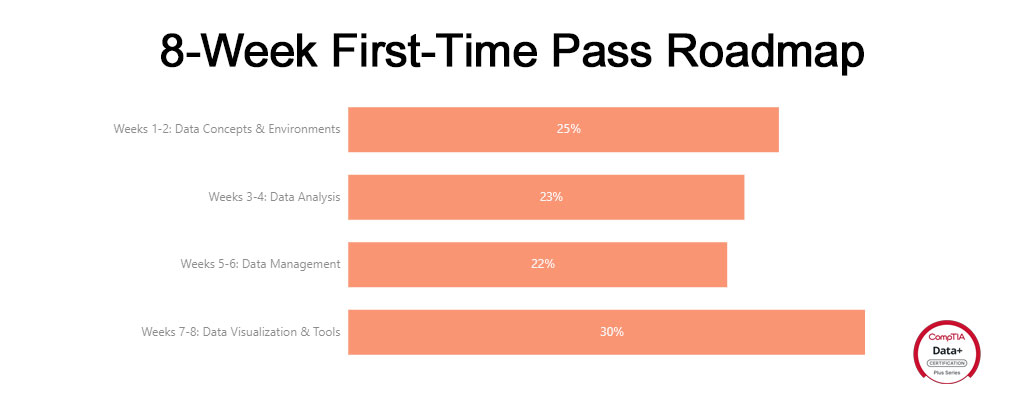
- Data+ → analytics-focused
Cloud+ is the most operations-driven.
It’s closest to what you actually do day-to-day.
Real Career Value
If you’re already working in cloud or systems:
Yes, it’s worth it.
Not because recruiters care (some do, some don’t), but because:
- It forces you to think holistically
- It connects dots across domains
- It exposes weak spots you didn’t know you had
Conclusion
Passing Cloud+ CV0-004 in 10 days is doable — but only if you already have real-world experience.
This is not a beginner-friendly certification.
It’s messy, ambiguous, and sometimes frustrating.
But that’s also why it’s valuable.
Because real cloud environments are exactly the same.
FAQs
1. Is 10 days enough to pass Cloud+ CV0-004?
If you already have 3–5 years of cloud or sysadmin experience, yes. Otherwise, it’s risky.
2. How hard is Cloud+ compared to Security+?
Cloud+ is harder in terms of decision-making and troubleshooting, while Security+ is more knowledge-based.
3. Are PBQs difficult in CV0-004?
Yes. They simulate real-world troubleshooting and can take significant time.
4. Do I need to know AWS/Azure specifics?
Not deeply, but you should understand general concepts across platforms.
5. What’s the passing score?
You need 750 out of 900 to pass