
I learned about this exam because I had a chat with the Manager in 2023, and he mentioned that I should take the most basic and “simple” exam of CompTIA—Security+.
Because they are all multiple-choice questions, 90 questions in 90 minutes, it is very simple in his eyes, especially compared to other advanced security certifications. There is no need to do a lab, set up an environment, or analyze cases, and it is very user-friendly. For students who have just graduated, it is also readily available.
Although I say this, since I took Cisco’s basic network course in college and passed the CCENT exam, I have almost forgotten the basic knowledge related to networks.
This Security+ covers network security-related topics based on network knowledge, such as common network attacks, protocols, encryption risk management, etc.
From 2022 to the first half of 2023, I was actively preparing for CCL and PTE, and it took me more than a year to have the energy to cope with CompTIA. Next, I will briefly record my preparation process. Some experiences are for reference only.
Security+ 601 or 701?
Since technology is changing with each passing day, the exam will also be updated to adapt to the trends of the times, just like the iPhone is released every year.
CompTIA stipulates that when a version is launched on the market, it will usually be withdrawn from the stage of history three years later. 601 was launched in 2020. It will officially announce its retirement in July 2024 and will not accept registration.
At the same time, his successor is 701. However, CompTIA will introduce successors to the market early to warm up, so 701 can already be taken in November 2023.
SY0-601 and SY0-701 Domains Compared
When I signed up, I was a little hesitant whether to apply for the latest 701 or the more mature 601.
Because the versions are different, the content involved is also different.
In general:
The new CompTIA Security+ (SY0-701) addresses the latest cybersecurity trends and techniques – covering the most core technical skills in risk assessment and management, incident response, forensics, enterprise networks, hybrid/cloud operations, and security controls, ensuring high performance on the job. These skills include:
- Assessing the security posture of an enterprise environment and recommending and implementing appropriate security solutions.
- Monitoring and securing hybrid environments, including cloud, mobile, Internet of Things (IoT), and operational technology (OT).
- Operating with an awareness of applicable regulations and policies, including principles of governance, risk, and compliance.
- Identifying, analyzing, and responding to security events and incidents.
And 20% of exam objectives were updated to include:
- Current trends: The latest trends in threats, attacks, vulnerabilities, automation, zero trust, risk, IoT, OT, and cloud environments are emphasized, as well as communication, reporting, and teamwork.
- Hybrid environments: The latest techniques for cybersecurity professionals working in hybrid environments that are located in the cloud and on-premises; cybersecurity professionals should be familiar with both worlds.
Let’s take a look at the differences between the 601 and 701 exam domains:
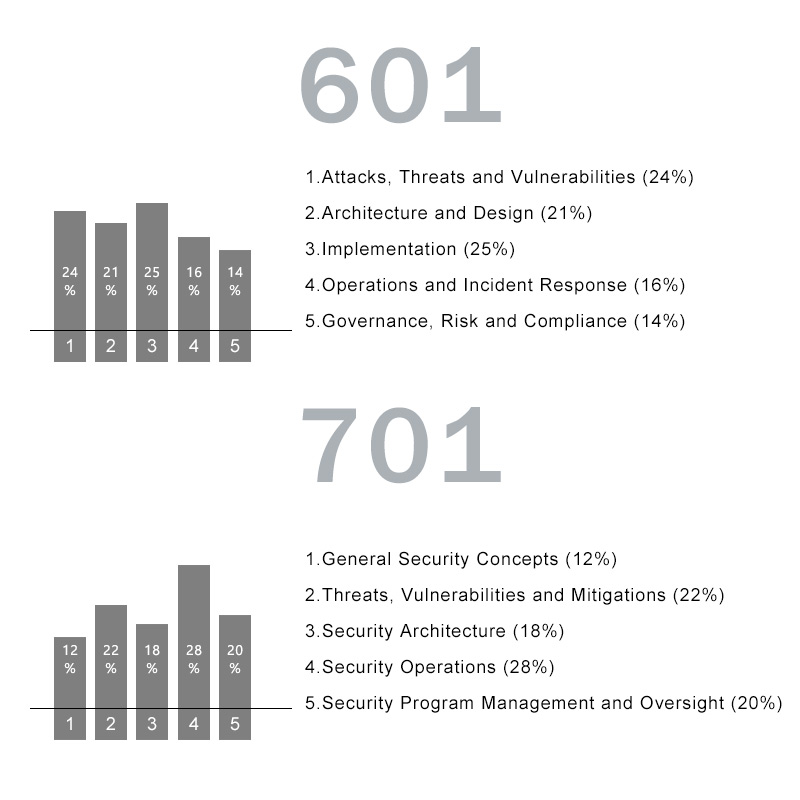
Let’s go through each SY0-701 domain and what each encompasses.
1. General Security Concepts (12%)
This domain dives into the foundational aspects of security, including the CIA triad of Confidentiality, Integrity, and Availability. It also introduces various types of security controls like preventive, deterrent, and corrective, and the Zero Trust architecture.
2. Threats, Vulnerabilities, and Mitigations (22%)
This domain focuses on identifying and understanding common threat actors and their motivations, such as nation-states and hacktivists. It also discusses various threat vectors like email, SMS, and vulnerable software.
3. Security Architecture (18%)
This domain centers on secure systems architecture, discussing data types, classifications, and methods to secure data. It also covers high availability considerations like load balancing and site considerations like geographic dispersion.
4. Security Operations (28%)
This is the most heavily weighted domain and covers a wide range of operational activities, including incident response and the importance of automation and orchestration in secure operations. It also discusses using various data sources like logs and vulnerability scans to support security investigations.
5. Security Program Management and Oversight (20%)
This domain focuses on the governance aspects of security, summarizing elements of effective security governance like policies and standards. It also goes into risk management processes, strategies, and security awareness practices like phishing recognition and user training.
Exam Registration
I chose CompTIA Security+ 701.
The next step is to register. It is said that books cannot be read unless they are borrowed, so if you don’t pay and set a time for the exam, you won’t start preparing with all your heart. The scariest thing is not having a deadline, because I always feel like I have time, so I have to be ready before I sign up for the exam.
Realizing that I had delayed for several months, I resolutely clicked on the CompTIA official website to register in December 2023.
The steps for me to register for the exam were a bit detoured. I bought a voucher from the CompTIA official website and then went to Pearson Vue to arrange the exam. You can register directly with Pearson Vue, schedule the exam, and then pay.
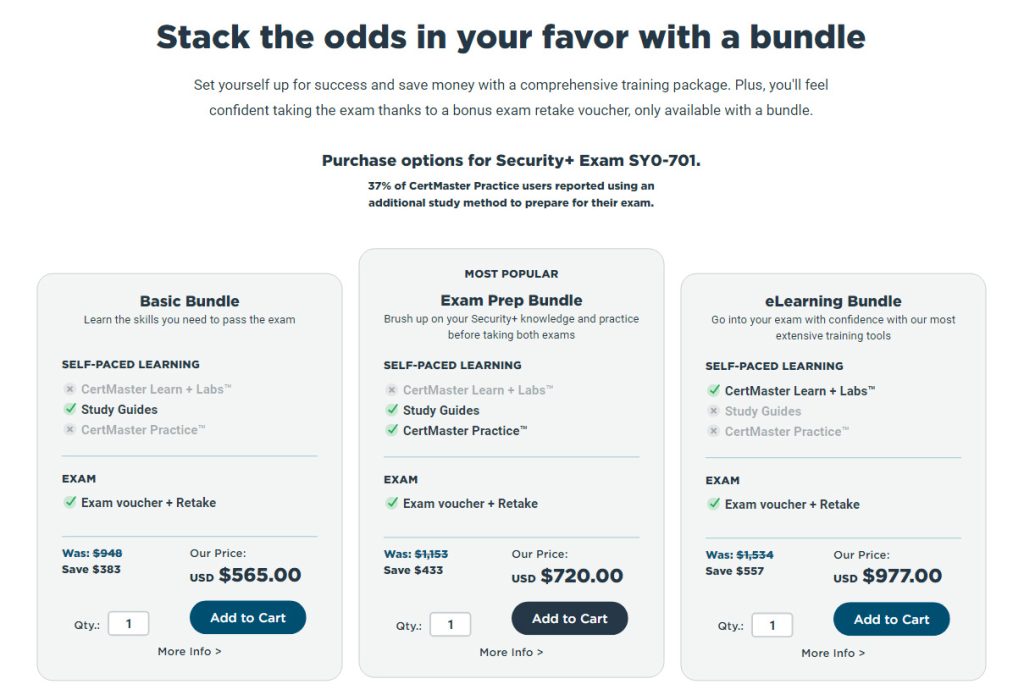
The advantage of buying a voucher from the official website is that there are different combinations to choose from, such as training courses, simulation questions, e-books, and re-exams. If you just want to schedule the exam quickly, you can skip step 1 and go to step 2. Go to PearsonVUE to schedule the exam.
1. Go to CompTIA’s official website to buy the voucher
First, I went to the CompTIA official website in the exam area to purchase exam coupons: go to https://store.comptia.org/ to register – login
Then, select Certification Vouchers – check Security+, and you will see that there are currently two versions of Security+ to choose from, with the same price:
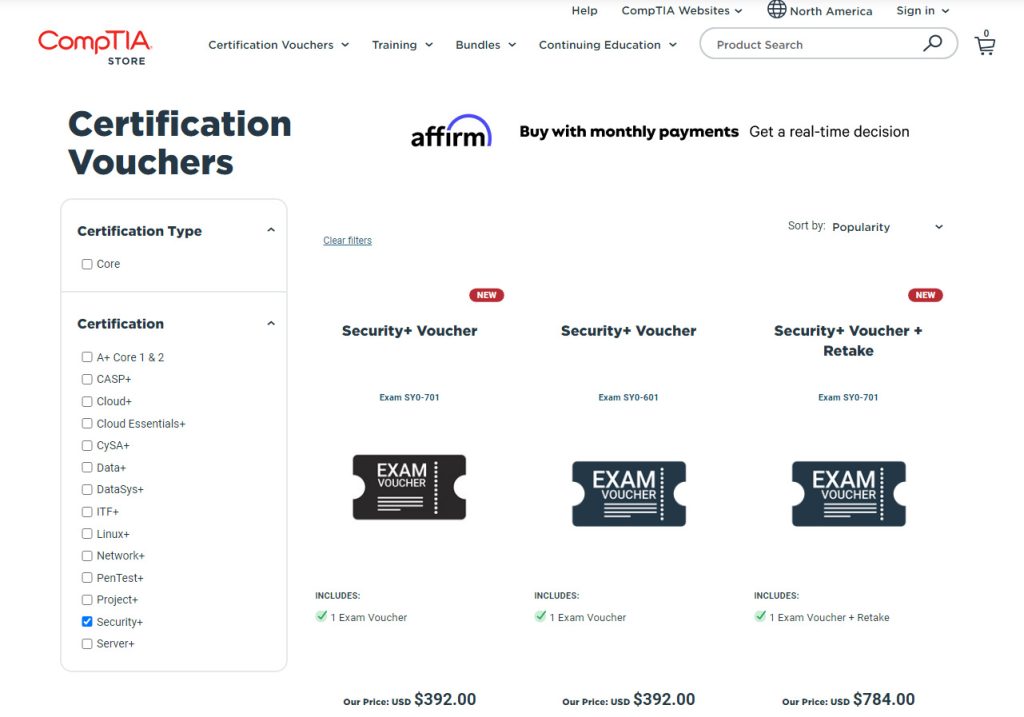
Then, enter the version you want to take, taking 701 as an example, click Details:
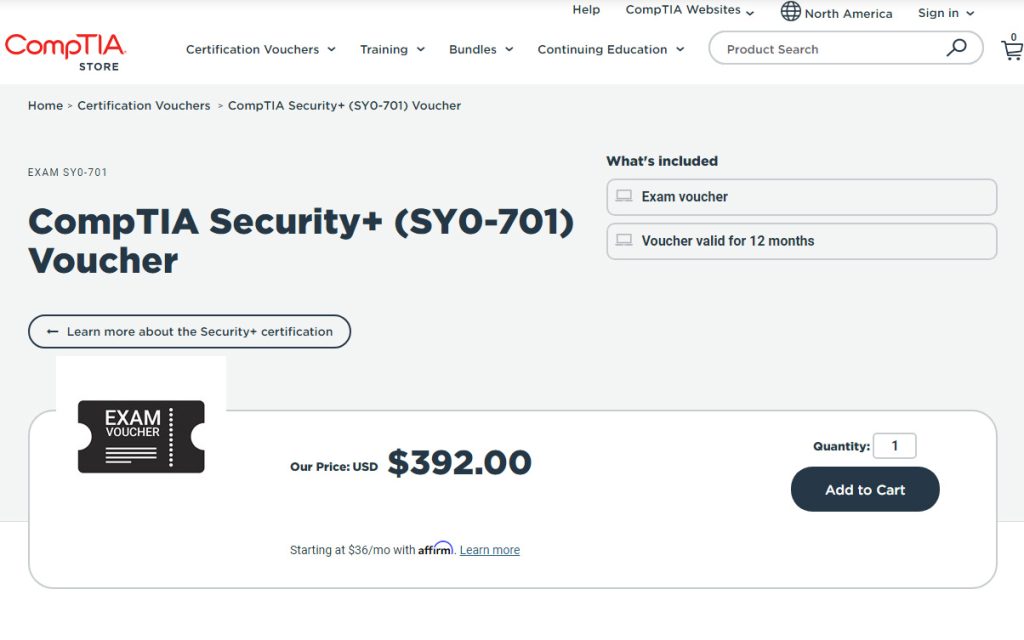
You will see that there are different combinations to choose from, each containing different products. Scroll down to see the specific information of each bundle. Here I chose the first one simply and rudely, because I felt that I should be able to pass it once without a Retake (the official website also provides training courses, but I have not used them, and I don’t know if they will be as lengthy as the official AWS training).
Then add to cart – pay. Remember, don’t forget to fill in the discount code for children’s shoes, as there is a 10% discount. How to get the discount code will be mentioned later!
After the payment is successful, you will receive an email stating that you have successfully purchased the voucher, and then you will receive the voucher code through another email. So the question is, I just bought a voucher for so long. When and where should I take the exam? How do I book a test?
Because many of these certificate exams are outsourced, you usually go to a Pearson VUE Test Center to take these exams. So, if you check your purchase record at this time, you will see that you have successfully purchased Security+, but you need to go to another place to arrange your exam.
Find your historical order, your voucher information will be displayed on it, then go to Pearson to confirm the exam time and location.
2. Go to PearsonVUE to schedule the exam
CompTIA Pearson vue registration: https://home.pearsonvue.com/Clients/CompTIA.aspx
Go to Pearson CompTIA homepage:
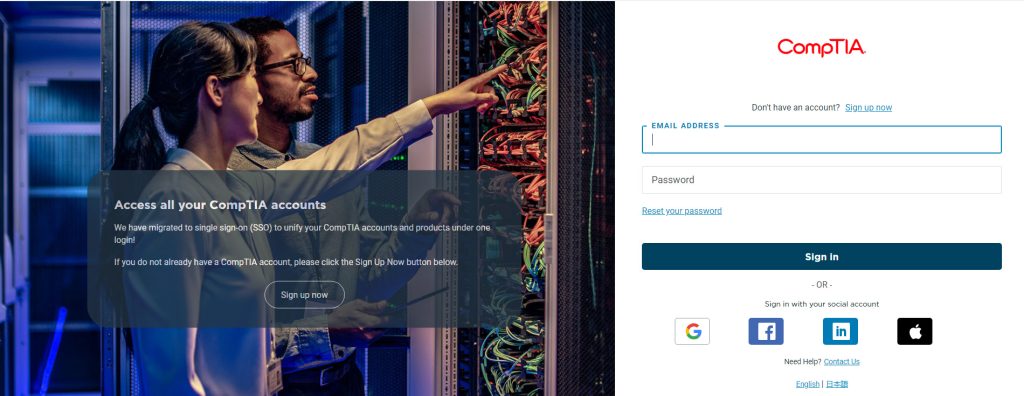
After successful registration, enter the homepage of Pearson CompTIA
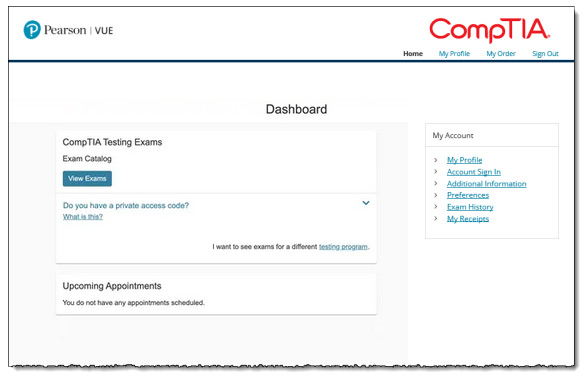
All Step:
- Select Exam: Security+
- Choose the exam code. Generally, there will be only one, unless it is in a transitional period like Security+ 601. The test I took this time was SY0-701.
- Currently, many exams provide two options: going to a test center (Test Center) and taking the test at home. However, I heard that there were too many reasons why personal computers could not be connected, network problems, system problems, etc., so I chose to go to the exam center without fear of trouble. Of course, this varies from person to person. If there is no test center near your home and you don’t want to spend time traveling, then the best option is to take the test at home.
- Select language
- The next step is to confirm the exam interface, make sure you select the one you want to take, and then the price will be displayed.
- The next step is to find a nearby test center
- Select your ideal date and time
- The last step is to pay, enter a voucher code
Since you have already paid on the CompTIA official website, you only need to fill in the voucher code you just received from the CompTIA official website, and you can place an order successfully! Pearson will then email you the test center date and time.
Useful lessons for exam preparation
My preparation process mainly consisted of taking online classes and answering questions at the same time. I recommend this course called Mike Chapple on LinkedIn Learning.
https://www.linkedin.com/learning/topics/comptia
I have also watched some videos on YouTube, but many of them will complicate things. I can explain a concept to you for 20 to 30 minutes.
For candidates with some basic knowledge, it will be a waste of time. Mike’s courses simply and clearly explain to you the knowledge points involved in the exam and directly highlight the key points to remind you of the minefields in the exam, which is simply a blessing for exam fast-foodists like me.
However, this course is more suitable for candidates who have a certain foundation of network knowledge.
If you are a newbie, I recommend this course from CB Nuggets:
https://www.cbtnuggets.com/it-training/comptia/security-plus
Keith Barker, the lecturer in this class, is quite humorous and can stir up the atmosphere, so you are less likely to feel drowsy because the content is extremely boring. His course covers a comprehensive range of topics and explains them in detail, including some basic knowledge of Networking such as the OSI model, how to classify IPs, VLANs, etc.
The above are all paid courses that require you to subscribe (monthly or yearly). But LinkedIn will have a 1-month free trial, you can take advantage of it for “free sex” ~~~ At the same time, when you use LinkedIn, remember to download the exam coupon (a PDF document) from Mike Chapple’s course page, at Enter the discount code when registering to get a 10% discount!!!
Preparation materials (mainly exam practice)
Because I thought Mike Chapple spoke very well, I was naturally moved by him and bought his Last Minute Review ($9.99).
This PDF document condenses the important knowledge points involved in the entire exam into 13 pages. You can ask for confirmation when you don’t understand something when answering questions. It helps consolidate knowledge points during the preparation process and quickly browse and memorize before the exam. My feeling is that every word may be a test point.
However, the Last Minute Review I bought at that time was not very comprehensive. I felt that some knowledge points were missing, so I also added a lot of things, which is equivalent to making a complete and unified arrangement.
At the same time, the most important thing is to use the existing question bank. There are many test bank websites for various certificates on the Internet, and some of them are paid. I mainly use Leads4Pass.
It has multiple purchase methods, namely PDF and VCE. I paid $45.99 to read the full version of Question 701.
https://www.leads4pass.com/sy0-701.html
At present, it does not provide free test questions. I saw that other test codes provide free test questions, so I consulted customer service.
She told me that because sy0-701 is the latest exam item, free exam questions are not available for the time being.
The preparation process is a cycle of exam practice, summarizing mistakes, reviewing knowledge points – practice tests – summary – review. If you don’t understand anything, you can refer to Leads4Pass, and then watch the relevant course video explanations. If you are still not sure, just Google it.
…
Since time is limited and there is still a lot to express, I will write a separate article about the entire exam process next time! If you find it helpful, please bookmark and follow it! Thanks!

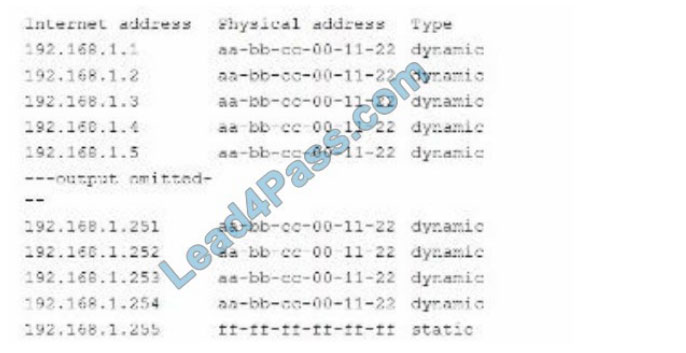



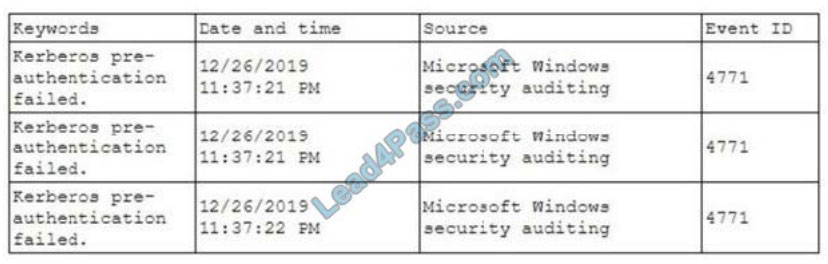
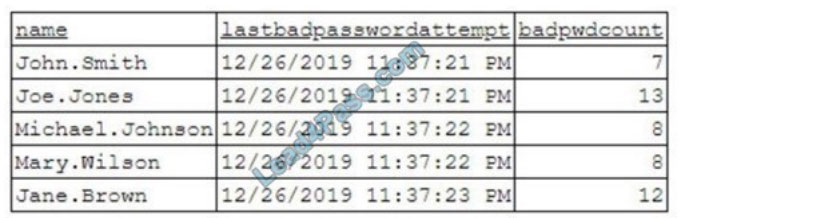
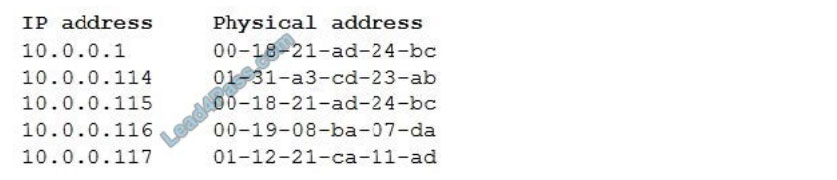


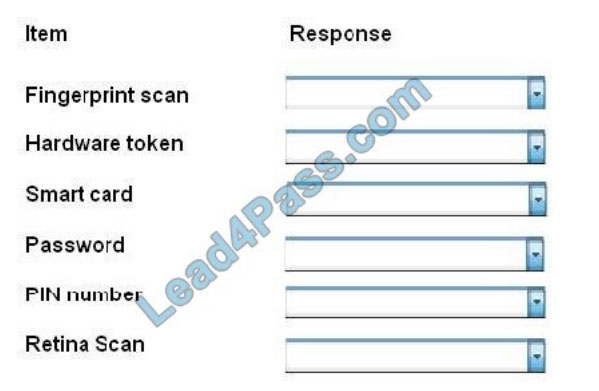

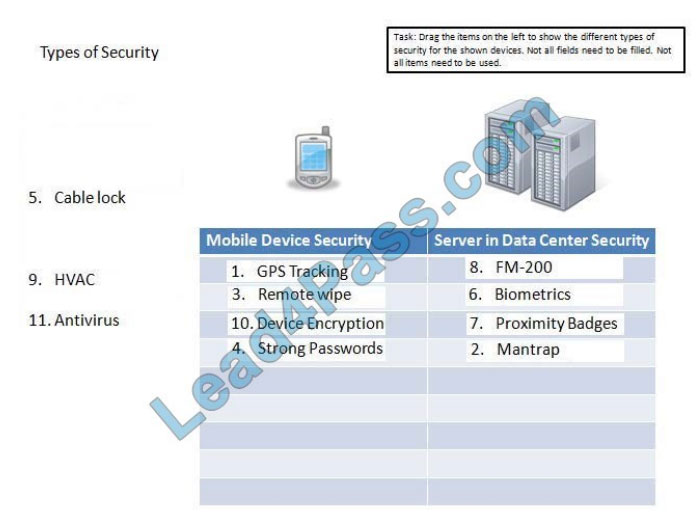

![[2021.3] lead4pass sy0-601 practice test q2](https://www.braindump4it.com/wp-content/uploads/2021/03/q2-4.jpg)
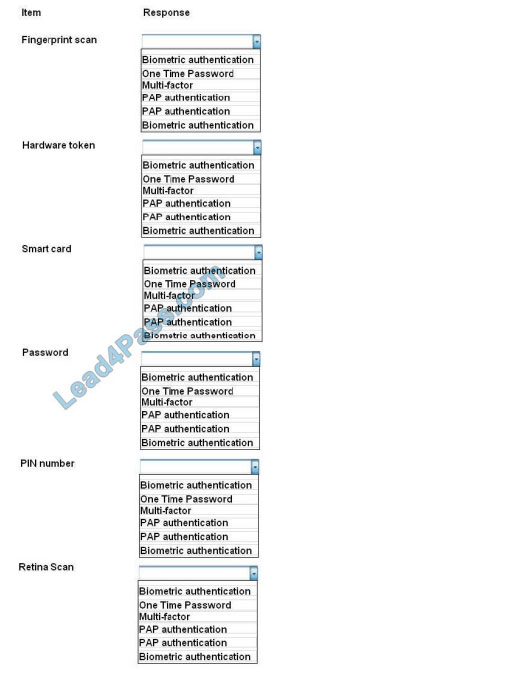
![[2021.3] lead4pass sy0-601 practice test q2-1](https://www.braindump4it.com/wp-content/uploads/2021/03/q2-1-1.jpg)
![[2021.3] lead4pass sy0-601 practice test q2-2](https://www.braindump4it.com/wp-content/uploads/2021/03/q2-2-1.jpg)
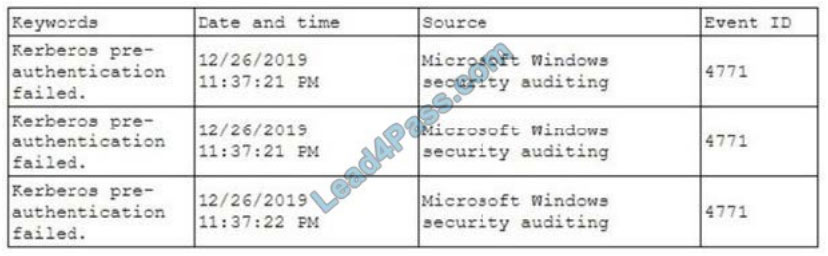
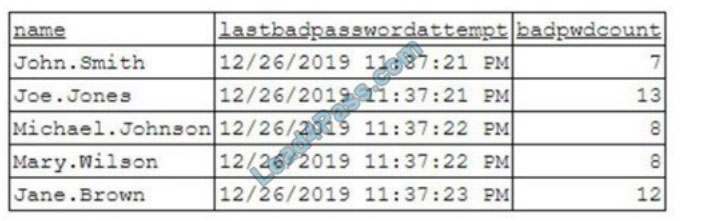
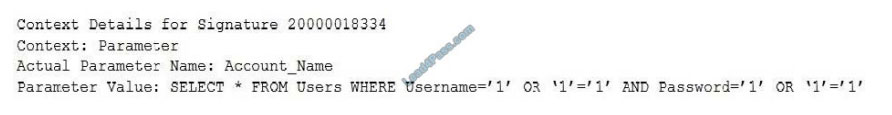
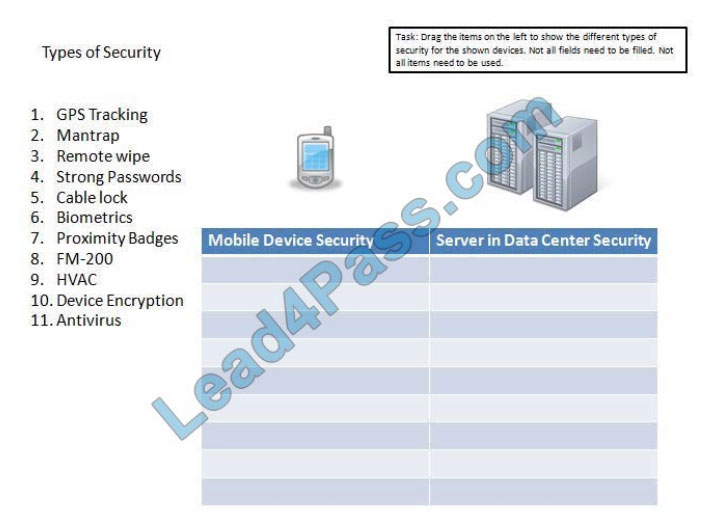
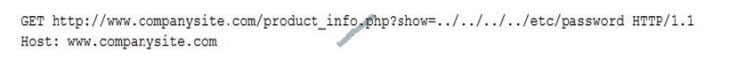
![[2021.3] lead4pass sy0-601 practice test q9](https://www.braindump4it.com/wp-content/uploads/2021/03/q9.jpg)
![[2021.3] lead4pass sy0-601 practice test q9-1](https://www.braindump4it.com/wp-content/uploads/2021/03/q9-1.jpg)
![[2021.3] lead4pass sy0-601 practice test q9-3](https://www.braindump4it.com/wp-content/uploads/2021/03/q9-3.jpg)
![[2021.3] lead4pass sy0-601 practice test q9-2](https://www.braindump4it.com/wp-content/uploads/2021/03/q9-2.jpg)

![[2021.3] lead4pass sy0-501 practice test q3](https://www.braindump4it.com/wp-content/uploads/2021/03/q3.jpg)
![[2021.3] lead4pass sy0-501 practice test q10](https://www.braindump4it.com/wp-content/uploads/2021/03/q10.jpg)
![[2021.3] lead4pass sy0-501 practice test q10-1](https://www.braindump4it.com/wp-content/uploads/2021/03/q10-1.jpg)