
The latest updated and revised CompTIA SY0-601 exam questions and answers come from Lead4Pass! Complete CompTIA SY0-601 dumps certification questions!
Welcome to download the latest Lead4Pass CompTIA SY0-601 dumps with PDF and VCE: https://www.leads4pass.com/sy0-601.html (401 Q&A)
[CompTIA SY0-601 dumps pdf] CompTIA SY0-601 dumps PDF uploaded from Braindump4it, online download provided by the latest update of Lead4pass:
https://www.braindump4it.com/wp-content/uploads/2021/07/Lead4pass-CompTIA-Security-Plus-SY0-601-Exam-Dumps-Braindumps-PDF-VCE.pdf
Latest update CompTIA SY0-601 exam questions and answers online practice test
QUESTION 1
A document that appears to be malicious has been discovered in an email that was sent to a company\\’s Chief
Financial Officer (CFO). Which of the following would be BEST to allow a security analyst to gather information and
confirm it is a malicious document without executing any code it may contain?
A. Open the document on an air-gapped network
B. View the document\\’s metadata for origin clues
C. Search for matching file hashes on malware websites D. Detonate the document in an analysis sandbox
Correct Answer: D
QUESTION 2
A smart retail business has a local store and a newly established and growing online storefront. A recent storm caused
a power outage to the business and the local ISP, resulting in several hours of lost sales and delayed order processing.
The business owner now needs to ensure two things:
1.
Protection from power outages
2.
Always-available connectivity In case of an outage
The owner has decided to implement battery backups for the computer equipment Which of the following would BEST
fulfill the owner\\’s second need?
A. Lease a point-to-point circuit to provide dedicated access.
B. Connect the business router to its own dedicated UPS.
C. Purchase services from a cloud provider for high availability
D. Replace the business\\’s wired network with a wireless network.
Correct Answer: C
QUESTION 3
A security analyst has been asked to investigate a situation after the SOC started to receive alerts from the SIEM. The
analyst first looks at the domain controller and finds the following events: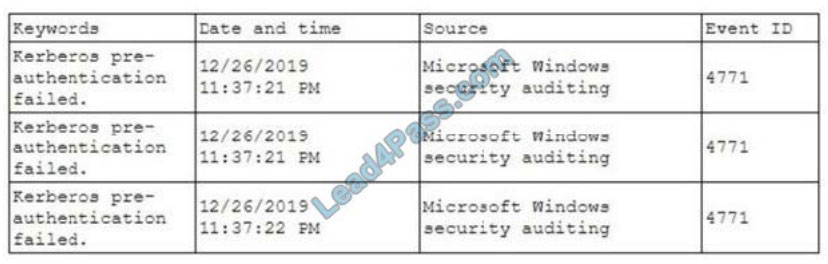
To better understand what is going on, the analyst runs a command and receives the following output:
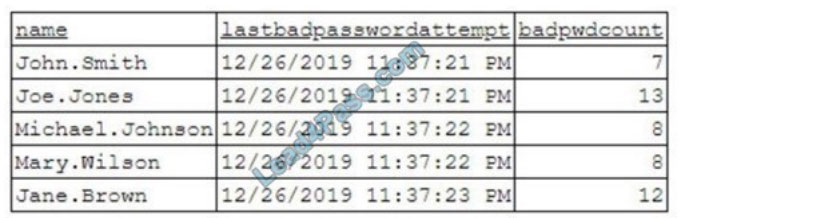
Based on the analyst\\’s findings, which of the following attacks is being executed?
A. Credential harvesting
B. Keylogger
C. Brute-force
D. Spraying
Correct Answer: D
QUESTION 4
Phishing and spear-phishing attacks have been occurring more frequently against a company\\’s staff. Which of the
following would MOST likely help mitigate this issue?
A. DNSSEC and DMARC
B. DNS query logging
C. Exact mail exchanger records in the DNS
D. The addition of DNS conditional forwarders
Correct Answer: C
QUESTION 5
A security analyst is reviewing information regarding recent vulnerabilities. Which of the following will the analyst MOST
likely consult to validate which platforms have been affected?
A. OSINT
B. SIEM
C. CVSS
D. CVE
Correct Answer: D
QUESTION 6
A local coffee shop runs a small WiFi hotspot for its customers that utilizes WPA2-PSK. The coffee shop would like to
stay current with security trends and wants to implement WPA3 to make its WiFi even more secure. Which of the
following technologies will the coffee shop MOST likely use in place of PSK?
A. WEP
B. MSCHAP
C. WPS
D. SAE
Correct Answer: D
QUESTION 7
A security analyst is investigating an incident that was first reported as an issue connecting to network shares and the
Internet. While reviewing logs and tool output, the analyst sees the following: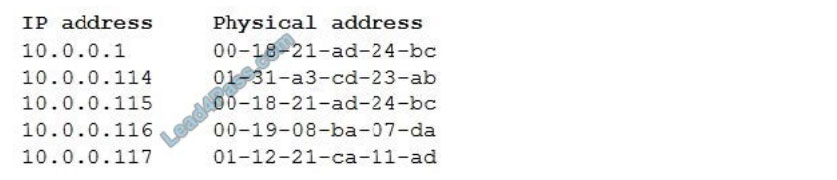
Which of the following attacks has occurred?
A. IP conflict
B. Pass-the-hash
C. MAC flooding
D. Directory traversal
E. ARP poisoning
Correct Answer: E
QUESTION 8
A website developer is working on a new e-commerce website and has asked an information security expert for the
most appropriate way to store credit card numbers to create an easy reordering process. Which of the following
methods would BEST accomplish this goal?
A. Salting the magnetic strip information
B. Encrypting the credit card information in transit.
C. Hashing the credit card numbers upon entry.
D. Tokenizing the credit cards in the database
Correct Answer: C
QUESTION 9
A company is implementing MFA for all applications that store sensitive data. The IT manager wants MFA to be nondisruptive and user friendly. Which of the following technologies should the IT manager use when implementing MFA?
A. One-time passwords
B. Email tokens
C. Push notifications D. Hardware authentication
Correct Answer: C
QUESTION 10
After reading a security bulletin, a network security manager is concerned that a malicious actor may have breached the
network using the same software flaw. The exploit code is publicly available and has been reported as being used
against other industries in the same vertical. Which of the following should the network security manager consult FIRST
to determine a priority list for forensic review?
A. The vulnerability scan output
B. The IDS logs
C. The full packet capture data
D. The SIEM alerts
Correct Answer: A
QUESTION 11
A network engineer is troubleshooting wireless network connectivity issues that were reported by users. The issues are
occurring only in the section of the building that is closest to the parking lot. Users are intermittently experiencing slow
speeds when accessing websites and are unable to connect to network drives. The issues appear to increase when
laptop users return desks after using their devices in other areas of the building. There have also been reports of users
being required to enter their credentials on web pages in order to gain access to them. Which of the following is the
MOST likely cause of this issue?
A. An external access point is engaging in an evil-twin attack.
B. The signal on the WAP needs to be increased in that section of the building.
C. The certificates have expired on the devices and need to be reinstalled.
D. The users in that section of the building are on a VLAN that is being blocked by the firewall.
Correct Answer: A
QUESTION 12
A cybersecurity department purchased o new PAM solution. The team is planning to randomize the service account
credentials of the Windows server first. Which of the following would be the BEST method to increase the security on
the Linux server?
A. Randomize the shared credentials
B. Use only guest accounts to connect.
C. Use SSH keys and remove generic passwords
D. Remove all user accounts.
Correct Answer: C
QUESTION 13
Which of the following algorithms has the SMALLEST key size?
A. DES
B. Twofish
C. RSA
D. AES
Correct Answer: B
QUESTION 14
A network administrator needs to build out a new datacenter, with a focus on resiliency and uptime. Which of the
following would BEST meet this objective? (Choose two.)
A. Dual power supply
B. Off-site backups
C. Automatic OS upgrades
D. NIC teaming
E. Scheduled penetration testing
F. Network-attached storage
Correct Answer: AB
QUESTION 15
Which of the following would be BEST to establish between organizations that have agreed cooperate and are engaged
in early discussion to define the responsibilities of each party, but do not want to establish a contractually binding
agreement?
A. An SLA
B. AnNDA
C. ABPA
D. AnMOU
Correct Answer: D
Update the latest valid CompTIA SY0-601 test questions and answers throughout the year.
Upload the latest SY0-601 exam practice questions and SY0-601 PDF for free every month. Get the complete SY0-601 Brain Dumps, the latest updated exam questions and answers come from Lead4Pass! For information about Lead4pass SY0-601 Dumps (including PDF and VCE),
please visit: https://www.leads4pass.com/sy0-601.html (PDF + VCE)
ps. Get free CompTIA SY0-601 dumps PDF online: https://www.braindump4it.com/wp-content/uploads/2021/07/Lead4pass-CompTIA-Security-Plus-SY0-601-Exam-Dumps-Braindumps-PDF-VCE.pdf