
The Cisco 350-701 SCOR certification exam is the only core Cisco CCNP Security exam designed to validate your knowledge of implementing and operating core security technologies.
Use Lead4Pass 350-701 dumps: https://www.leads4pass.com/350-701.html to take the 350-701 SCOR certification exam and make sure you pass the exam 100%.
Lead4Pass 350-701 dumps come with PDF and VCE practice formats, you can choose any because both types contain the latest exam questions and answers! And 598 exam questions and answers were updated in April, Available for full-year 2023 certification exams! (Because Lead4Pass 350-701 dumps are updated throughout the year).
The more important surprise is! Share a part of Lead4Pass 350-701 dumps for free Download online: https://drive.google.com/file/d/15GyKUl66e6Hwlb6CKr2bqEMchQBeVRQ8/
You can also take the 350-701 online practice test
| From | Type | Answers | Last updated |
| Lead4Pass | Free | View | 350-701 dumps |
Question 1:
A user has a device in the network that is receiving too many connection requests from multiple machines.
Which type of attack is the device undergoing?
A. phishing
B. slow loris
C. pharming
D. SYN flood
Question 2:
An administrator is configuring N IP on Cisco ASA via ASDM and needs to ensure that rogue NTP servers cannot insert themselves as the authoritative time source Which two steps must be taken to accomplish this task? (Choose two)
A. Specify the NTP version
B. Configure the NTP stratum
C. Set the authentication key
D. Choose the interface for syncing to the NTP server
E. Set the NTP DNS hostname
Question 3:
Which Cisco security solution stops exfiltration using HTTPS?
A. Cisco FTD
B. Cisco AnyConnect
C. Cisco CTA
D. Cisco ASA
Question 4:
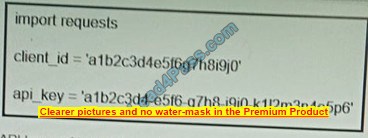
Refer to the exhibit. What function does the API key perform while working with https://api.amp.cisco.com/v1/computers?
A. imports requests
B. HTTP authorization
C. HTTP authentication
D. plays dent ID
Question 5:
What is the primary role of the Cisco Email Security Appliance?
A. Mail Submission Agent
B. Mail Transfer Agent
C. Mail Delivery Agent
D. Mail User Agent
Question 6:
What is the most common type of data exfiltration that organizations currently experience?
A. HTTPS file upload site
B. Microsoft Windows network shares
C. SQL database injections
D. encrypted SMTP
Question 7:
What is a description of micro-segmentation?
A. Environments apply a zero-trust model and specify how applications on different servers or containers can communicate
B. Environments deploy a container orchestration platform, such as Kubernetes, to manage the application delivery
C. Environments implement private VLAN segmentation to group servers with similar applications.
D. Environments deploy centrally managed host-based firewall rules on each server or container
Question 8:
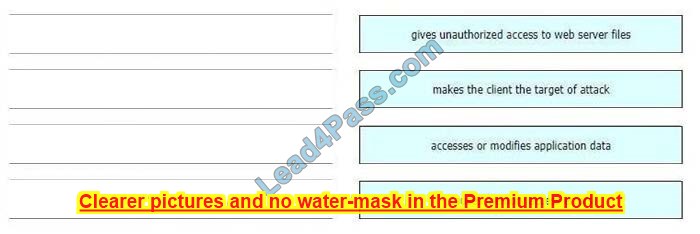
Drag and drop the exploits from the left onto the type of security vulnerability on the right.
Select and Place:
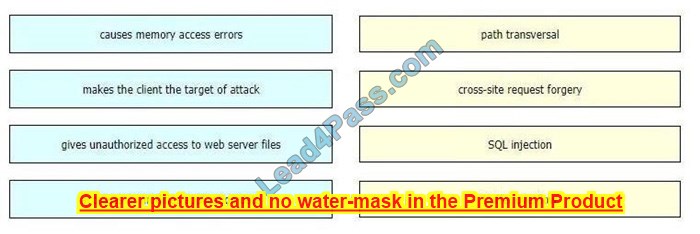
Correct Answer:
Question 9:
Which Cisco WSA feature supports access control using URL categories?
A. transparent user identification
B. SOCKS proxy services
C. web usage controls
D. user session restrictions
Question 10:
What is a feature of the open platform capabilities of Cisco DNA Center?
A. intent-based APIs
B. automation adapters
C. domain integration
D. application adapters
Question 11:
Which type of DNS abuse exchanges data between two computers even when there is no direct connection?
A. Malware installation
B. Command-and-control communication
C. Network footprinting
D. Data exfiltration
Reference: https://www.netsurion.com/articles/5-types-of-dns-attacks-and-how-to-detect-them
Question 12:
Which threat involves software being used to gain unauthorized access to a computer system?
A. virus
B. NTP amplification
C. ping of death
D. HTTP flood
Question 13:
Which API method and required attribute are used to add a device into DNAC with the native API?
A. lastSyncTime and paid
B. POST and name
C. userSudiSerialNos and devicelnfo
D. GET and serialNumber
To add a device to Cisco DNA Center with the native API, the API method used is POST which creates a new resource. One of the required attributes to add a device is the “name” attribute, which is used to specify the name of the device being added. The device name should be unique and it\’s used to identify the device within the Cisco DNA Center platform.
A GET request is used to retrieve information from a resource. “SerialNumber” and “userSudiSerialNos” are attributes used to identify a device but they are not required to add a device to Cisco DNA Center, they are needed to retrieve specific device information. “lastSyncTime” is an attribute used to indicate when the device last synced with Cisco DNA Center, it\’s not required to add a device. “pid” is an attribute used to identify a device\’s product ID, and it\’s not required to add a device.
Question 14:
Which two commands are required when configuring a flow-export action on a Cisco ASA? (Choose two.)
A. flow-export event-type
B. policy-map
C. access-list
D. flow-export template timeout-rate 15
E. access-group
Question 15:
DRAG DROP
Drag and drop the security solutions from the left onto the benefits they provide on the right.
Select and Place:
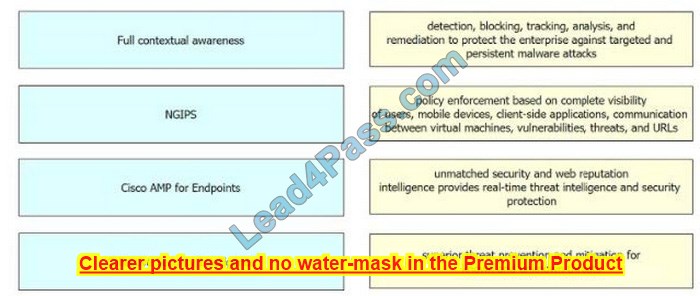
Correct Answer:
…
Verify answer:
| Questions: | Q1 | Q2 | Q3 | Q4 | Q5 | Q6 | Q7 | Q8 | Q9 | Q10 | Q11 | Q12 | Q13 | Q14 | Q15 |
| Answers: | D | CE | C | C | B | B | A | IMAGE | A | A | D | A | B | AB | IMAGE |
Summarize:
You can verify your current Cisco 350-701 studies online! You can also download some of the Lead4Pass 350-701 dumps online to help you progress!
But I recommend you to use the complete 350-701 SCOR dumps: https://www.leads4pass.com/350-701.html (598 Q&A)! Help you 100% successfully pass the only core exam of Cisco CCNP Security.