
Why choose Lead4Pass CAS-004 dumps?
Not all certification dump platforms can help you pass the exam 100%. Lead4Pass, Pass4sure, test-king, and Passleader are all established certification dumps platforms. They definitely stand among the best dumps platforms! I just want to tell the novice students the real situation here! Many experienced certification students know it. My topic today is CAS-004 dumps, and I will not introduce all dumps platforms one by one. But I want to tell you that the most cost-effective is Lead4pass. You can access these platforms, and I’m talking about the real situation.
There are still many new platforms appearing in front of everyone, I will not comment on them, but I can tell you that the most authoritative old websites are the above websites.
How to pass the CAS-004 exam?
Lead4Pass CAS-004 dumps https://www.leads4pass.com/cas-004.html(PDF +VCE). For both PDF and VCE learning modes. You can use either or both of these to help you learn the latest and most effective exam questions, which help You successfully pass the exam.
What is the difference between CAS-003 and CAS-004?
CAS-003 Published: April 2, 2018
Exam Description: CASP+ covers the technical knowledge and skills required to conceptualize, engineer, integrate and implement secure solutions across complex environments to support a resilient enterprise.
Retirement: April 5, 2022
CAS-004 Published: October 6, 2021
Exam Description: CASP+ covers the technical knowledge and skills required to architect, engineer, integrate, and implement secure solutions across complex environments to support a resilient enterprise while considering the impact of governance, risk, and compliance requirements.
Before you get a full CAS-004 dumps, you can also experience a small test in advance. I will share 12 CAS-004 test questions for free to help you test online, and the answers will be announced at the end of the test.
[Updated 2022.7] CAS-004 exam question and answers
QUESTION 1:
A security analyst is trying to identify the source of a recent data loss incident The analyst has reviewed all the logs for the time surrounding the incident and identified all the assets on the network at the time of the data loss. The analyst suspects the key to finding the source was obfuscated in an application.
Which of the following tools should the analyst use NEXT?
A. Software decompiler
B. Network enumerator
C. Log reduction and analysis tool
D. Static code analysis
Correct Answer: A
QUESTION 2:
A forensic investigator would use the foremost command for:
A. cloning disks.
B. analyzing network-captured packets.
C. recovering lost files.
D. extracting features such as email addresses.
Correct Answer: C
QUESTION 3:
A security analyst is performing a vulnerability assessment on behalf of a client. The analyst must define what constitutes a risk to the organization. Which of the following should be the analyst\’s FIRST action?
A. Create a full inventory of information and data assets.
B. Ascertain the impact of an attack on the availability of crucial resources.
C. Determine which security compliance standards should be followed.
D. Perform a full system penetration test to determine the vulnerabilities.
Correct Answer: C
QUESTION 4:
A developer wants to maintain the integrity of each module of a program and ensure the code cannot be altered by malicious users. Which of the following would be BEST for the developer to perform? (Choose two.)
A. Utilize code signing by a trusted third party.
B. Implement certificate-based authentication.
C. Verify MD5 hashes.
D. Compress the program with a password.
E. Encrypt with 3DES.
F. Make the DACL read-only.
Correct Answer: AB
QUESTION 5:
A technician is reviewing the logs and notices a large number of files were transferred to remote sites over the course of three months. This activity then stopped. The files were transferred via TLS-protected HTTP sessions from systems that do not send traffic to those sites.
The technician will define this threat as:
A. a decrypting RSA using obsolete and weakened encryption attack.
B. a zero-day attack.
C. an advanced persistent threat.
D. an on-path attack.
Correct Answer: A
[Updated 2022.7] Get more CompTIA CAS-004 exam questions and answers
CAS-004 Exam Questions Online Test
CAS-004 Q1:
A security analyst sees some suspicious entries in a log file from a web server website, which has a form that allows customers to leave feedback on the company\\’s products. The analyst believes a malicious actor is scanning the web form. To know which security controls to put in place, the analyst first needs to determine the type of activity occurring to design a control. Given the log below:
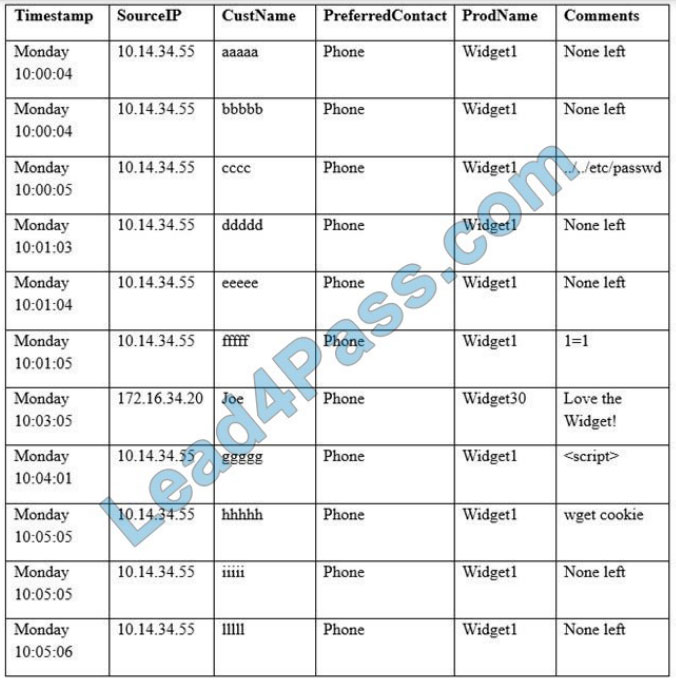
Which of the following is the MOST likely type of activity occurring?
A. SQL injection
B. XSS scanning
C. Fuzzing
D. Brute forcing
CAS-004 Q2:
The Information Security Officer (ISO) believes that the company has been targeted by cybercriminals and it is under a cyber attack. Internal services that are normally available to the public via the Internet are inaccessible, and employees in the office are unable to browse the Internet. The senior security engineer starts by reviewing the bandwidth at the border router, and notices that the incoming bandwidth on the router\\’s external interface is maxed out. The security engineer then inspects the following piece of log to try and determine the reason for the downtime, focusing on the company\\’s external router\\’s IP which is 128.20.176.19: 11:16:22.110343 IP 90.237.31.27.19 >
128.20.176.19.19: UDP, length 1400 11:16:22.110351 IP 23.27.112.200.19 >
128.20.176.19.19: UDP, length 1400 11:16:22.110358 IP 192.200.132.213.19 >
128.20.176.19.19: UDP, length 1400 11:16:22.110402 IP 70.192.2.55.19 >
128.20.176.19.19: UDP, length 1400 11:16:22.110406 IP 112.201.7.39.19 >
128.20.176.19.19: UDP, length 1400 Which of the following describes the findings the senior security engineer should report to the ISO and the BEST solution for service restoration?
A. After the senior engineer used a network analyzer to identify an active Fraggle attack, the company\\’s ISP should be contacted and instructed to block the malicious packets.
B. After the senior engineer used the above IPS logs to detect the ongoing DDOS attack, an IPS filter should be enabled to block the attack and restore communication.
C. After the senior engineer used a mirror port to capture the ongoing amplification attack, a BGP sinkhole should be configured to drop traffic at the source networks.
D. After the senior engineer used a packet capture to identify an active Smurf attack, an ACL should be placed on the company\\’s external router to block incoming UDP port 19 traffic.
The exhibit displays logs that are indicative of an active fraggle attack. A Fraggle attack is similar to a smurf attack in that it is a denial of service attack, but the difference is that a fraggle attack makes use of ICMP and UDP ports 7 and 19. Thus when the senior engineer uses a network analyzer to identify the attack he should contact the company\\’s ISP to block those malicious packets.
CAS-004 Q3:
Given the following output from a security tool in Kali:
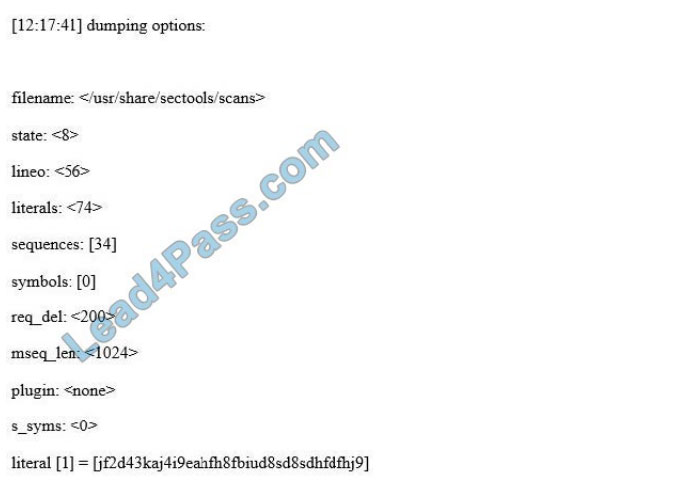
A. Log reduction
B. Network enumerator
C. Fuzzer
D. SCAP scanner
CAS-004 Q4:
An organization relies heavily on third-party mobile applications for official use within a BYOD deployment scheme An excerpt from an approved text-based-chat client application AndroidManifest xml is as follows:
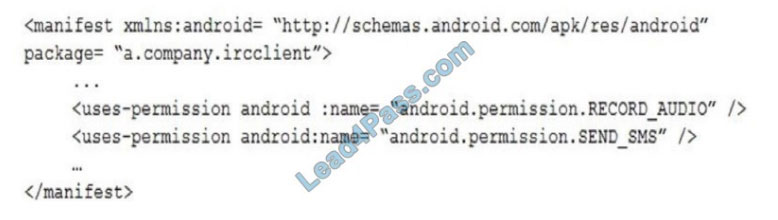
Which of the following would restrict application permissions while minimizing the impact to normal device operations?
A. Add the application to the enterprise mobile whitelist.
B. Use the MDM to disable the devices\\’ recording microphones and SMS.
C. Wrap the application before deployment.
D. Install the application outside of the corporate container.
CAS-004 Q5:
A small retail company recently deployed a new point of sale (POS) system to all 67 stores. The core of the POS is an extranet site, accessible only from retail stores and the corporate office over a split-tunnel VPN. An additional splittunnel VPN provides bi-directional connectivity back to the main office, which provides voice connectivity for store VoIP phones. Each store offers guest wireless functionality, as well as employee wireless. Only the staff wireless network has access to the POS VPN. Recently, stores are reporting poor response times when accessing the POS application from store computers as well as degraded voice quality when making phone calls. Upon investigation, it is determined that three store PCs are hosting malware, which is generating excessive network traffic. After malware removal, the information security department is asked to review the configuration and suggest changes to prevent this from happening again. Which of the following denotes the BEST way to mitigate future malware risk?
A. Deploy new perimeter firewalls at all stores with UTM functionality.
B. Change antivirus vendors at the store and the corporate office.
C. Move to a VDI solution that runs offsite from the same data center that hosts the new POS solution.
D. Deploy a proxy server with content filtering at the corporate office and route all traffic through it.
A perimeter firewall is located between the local network and the Internet where it can screen network traffic flowing in and out of the organization. A firewall with unified threat management (UTM) functionalities includes anti-malware capabilities.
CAS-004 Q6:
A technician is reviewing the following log:
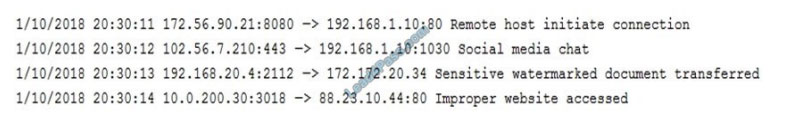
Which of the following tools should the organization implement to reduce the highest risk identified in this log?
A. NIPS
B. DLP
C. NGFW
D. SIEM
CAS-004 Q7:
To prepare for an upcoming audit, the Chief Information Security Officer (CISO) asks for all 1200 vulnerabilities on production servers to be remediated. The security engineer must determine which vulnerabilities represent real threats that can be exploited so resources can be prioritized to migrate the most dangerous risks. The CISO wants the security engineer to act in the same manner as would an external threat, while using vulnerability scan results to prioritize any actions.
Which of the following approaches is described?
A. Blue team
B. Red team
C. Black box
D. White team
CAS-004 Q8:
Which of the following are the MOST likely vectors for the unauthorized or unintentional inclusion of vulnerable code in a software company\\’s final software releases? (Choose two.)
A. Unsecure protocols
B. Use of penetration-testing utilities
C. Weak passwords
D. Included third-party libraries
E. Vendors/supply chain
F. Outdated anti-malware software
CAS-004 Q9:
During a system penetration test, a security engineer successfully gained access to a shell on a Linux host as a standard user and wants to elevate the privilege levels. Which of the following is a valid Linux post-exploitation method to use to accomplish this goal?
A. Spawn a shell using sudo and an escape string such as sudo vim -c ‘!sh’.
B. Perform ASIC password cracking on the host.
C. Read the /etc/passwd file to extract the usernames.
D. Initiate unquoted service path exploits.
E. Use the UNION operator to extract the database schema.
Reference: https://docs.rapid7.com/insightvm/elevating-permissions/
CAS-004 Q10:
Which of the following provides the BEST risk calculation methodology?
A. Annual Loss Expectancy (ALE) x Value of Asset
B. Potential Loss x Event Probability x Control Failure Probability
C. Impact x Threat x Vulnerability
D. Risk Likelihood x Annual Loss Expectancy (ALE)
Of the options given, the BEST risk calculation methodology would be Potential Loss x Event Probability x Control Failure Probability. This exam is about computer and data security so `loss\\’ caused by risk is not necessarily a monetary value.
For example:
Potential Loss could refer to the data lost in the event of a data storage failure.
Event probability could be the risk a disk drive or drives failing.
Control Failure Probability could be the risk of the storage RAID not being able to handle the number of failed hard drives without losing data.
CAS-004 Q11:
An IT manager is concerned about the cost of implementing a web filtering solution in an effort to mitigate the risks associated with malware and resulting data leakage. Given that the ARO is twice per year, the ALE resulting from a data leak is $25,000 and the ALE after implementing the web filter is $15,000. The web filtering solution will cost the organization $10,000 per year. Which of the following values is the single loss expectancy of a data leakage event after implementing the web filtering solution?
A. $0
B. $7,500
C. $10,000
D. $12,500
E. $15,000
The annualized loss expectancy (ALE) is the product of the annual rate of occurrence (ARO) and the single loss expectancy (SLE). It is mathematically expressed as: ALE = ARO x SLE Single Loss Expectancy (SLE) is
mathematically expressed as: Asset value (AV) x Exposure Factor (EF) SLE = AV x EF – Thus the Single Loss
Expectancy (SLE) = ALE/ARO = $15,000 / 2 = $ 7,500 References:
http://www.financeformulas.net/Return_on_Investment.html
https://en.wikipedia.org/wiki/Risk_assessment
CAS-004 Q12:
A company has expenenced negative publicity associated with users giving out their credentials accidentally or sharing intellectual secrets were not properly defined. The company recently implemented some new policies and is now testing their effectiveness. Over the last three months, the number of phishing victims-dropped from 100 to only two in the last test The DLP solution that was implemented catches potential material leaks, and the user responsible is retrained Personal email accounts and USB drives are restricted from the corporate network.
Given the improvements, which of the following would a security engineer identify as being needed in a gap analysis?
A. Additional corporate-wide training on phishing.
B. A policy outlining what is and is not acceptable on social media.
C. Notifications when a user falls victim to a phishing attack.
D. Positive DLP preventions with stronger enforcement.
Verify the answer:
| Q1 | Q2 | Q3 | Q4 | Q5 | Q6 | Q7 | Q8 | Q9 | Q10 | Q11 | Q12 |
| A | A | D | B | A | B | C | AC | C | B | B | B |
[Updated 2022.7]https://drive.google.com/file/d/1gPzIc5NxyzqTe5jbFzvmofpUGr5d4CUr/
PS. 12-track CAS-004 exam PDF free download:
https://drive.google.com/file/d/1mL0JwT4wlXDPb53aND7soRSLSfs6fGKd/view?usp=sharing
Complete CAS-004 Dumps Latest Update Feb 2022:https://www.leads4pass.com/cas-004.html (Total Questions: 255 Q&A) [Updated 2022.7] Total Questions: 267 Q&A. Participate in the full exam program and pass the exam 100% successfully.