The newly updated CompTIA PT0-002 dumps provides 162 exam questions and answers, covering the full range of practice exam questions, for all candidates taking the PT0-002 PenTest+ exam.
The CompTIA PT0-002 PenTest+ exam is for cybersecurity professionals responsible for penetration testing and vulnerability management, and you can use the PDF and VCE exam engine provided by the Lead4Pass PT0-002 dumps to learn all the exam knowledge to help you accomplish your mission.
Therefore, it is highly recommended that you use the latest updated PT0-002 dumps https://www.leads4pass.com/pt0-002.html, which guarantees you 100% success on the CompTIA PT0-002 PenTest+ exam.
Download the CompTIA PT0-002 PDF 2022:
https://drive.google.com/file/d/17L47_KDIP0cQJapPpfYFN5yjBJBkT3Wg/
Experience a selection of the latest CompTIA PT0-002 Dumps exam questions and answers
| Number of exam questions | Exam name | From | PDF Download |
| 13 | CompTIA PenTest+ Certification Exam | Lead4Pass | pt0-002 pdf |
NEW QUESTION 1:
A security assessor is attempting to craft specialized XML files to test the security of the parsing functions during ingest into a Windows application. Before beginning to test the application, which of the following should the assessor request from the organization?
A. Sample SOAP messages
B. The REST API documentation
C. A protocol fuzzing utility
D. An applicable XSD file
Correct Answer: D
NEW QUESTION 2:
User credentials were captured from a database during an assessment and cracked using rainbow tables. Based on the ease of compromise, which of the following algorithms was MOST likely used to store the passwords in the database?
A. MD5
B. bcrypt
C. SHA-1
D. PBKDF2
Correct Answer: A
Reference: https://www.geeksforgeeks.org/understanding-rainbow-table-attack/
NEW QUESTION 3:
A penetration tester is starting an assessment but only has publicly available information about the target company. The client is aware of this exercise and is preparing for the test. Which of the following describes the scope of the assessment?
A. Partially known environment testing
B. Known environment testing
C. Unknown environment testing
D. Physical environment testing
Correct Answer: C
NEW QUESTION 4:
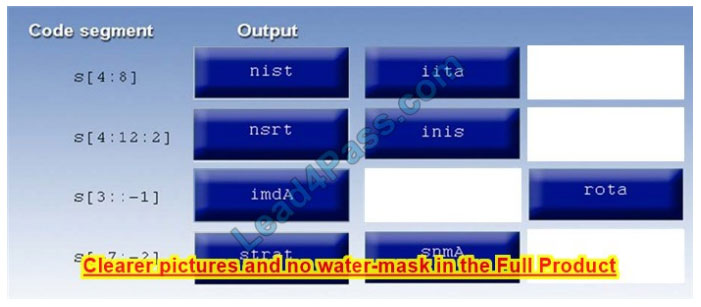
A manager calls upon a tester to assist with diagnosing an issue within the following:
Python script: #!/user/bin/python s = “Administrator”
The tester suspects it is an issue with string slicing and manipulation Analyze the following code segment and drag and drop the correct output for each string manipulation to its corresponding code segment Options may be used once or not at all.
Select and Place:
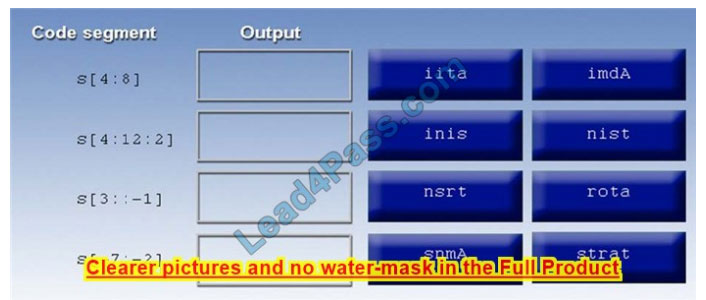
Correct Answer:
NEW QUESTION 5:
A penetration tester was conducting a penetration test and discovered the network traffic was no longer reaching the client\’s IP address. The tester later discovered the SOC had used a sinkhole on the penetration tester\’s IP address.
Which of the following BEST describes what happened?
A. The penetration tester was testing the wrong assets
B. The planning process failed to ensure all teams were notified
C. The client was not ready for the assessment to start
D. The penetration tester had incorrect contact information
Correct Answer: B
NEW QUESTION 6:
Running a vulnerability scanner on a hybrid network segment that includes general IT servers and industrial control systems:
A. will reveal vulnerabilities in the Modbus protocol.
B. may cause unintended failures in control systems.
C. may reduce the true positive rate of findings.
D. will create a denial-of-service condition on the IP networks.
Correct Answer: B
Reference: https://www.hsdl.org/?viewanddid=7262
NEW QUESTION 7:
A penetration tester ran a ping –A command during an unknown environment test, and it returned a 128 TTL packet.
Which of the following OSs would MOST likely return a packet of this type?
A. Windows
B. Apple
C. Linux
D. Android
Correct Answer: A
Reference: https://www.freecodecamp.org/news/how-to-identify-basic-internet-problems-with-ping/
NEW QUESTION 8:
A security team is switching firewall vendors. The director of security wants to scope a penetration test to satisfy the requirements to perform the test after major architectural changes. Which of the following is the BEST way to approach the project?
A. Design a penetration test approach, focusing on publicly released firewall DoS vulnerabilities.
B. Review the firewall configuration, followed by a targeted attack by a read team.
C. Perform a discovery scan to identify changes in the network.
D. Focus on an objective-based approach to assess network assets with a red team.
Correct Answer: D
NEW QUESTION 9:
When preparing for an engagement with an enterprise organization, which of the following is one of the MOST important items to develop fully prior to beginning the penetration testing activities?
A. Clarify the statement of work.
B. Obtain an asset inventory from the client.
C. Interview all stakeholders.
D. Identify all third parties involved.
Correct Answer: A
NEW QUESTION 10:
The results of a Nmap scan are as follows:
Starting Nmap 7.80 ( https://nmap.org ) at 2021-01-24 01:10 EST
Nmap scan report for ( 10.2.1.22 )
The host is up (0.0102s latency).
Not shown: 998 filtered ports
Port State Service
80/TCP open HTTP
|_http-title: 80F 22% RH 1009.1MB (text/HTML)
|_http-slowloris-check:
| VULNERABLE:
| Slowloris DoS Attack
|Device type: bridge|general purpose
Running (JUST GUESSING): QEMU (95%)
OS CPE: cpe:/a:qemu:qemu
No exact OS matches were found for the host (test conditions non-ideal).
OS detection was performed. Please report any incorrect results at https://nmap.org/submit/.
Nmap done: 1 IP address (1 host up) scanned in 107.45 seconds
Which of the following device types will MOST likely have a similar response? (Choose two.)
A. Network device
B. Public-facing web server
C. Active Directory domain controller
D. IoT/embedded device
E. Exposed RDP
F. Print queue
Correct Answer: AB
NEW QUESTION 11:
A software company has hired a penetration tester to perform a penetration test on a database server. The tester has been given a variety of tools used by the company\’s privacy policy. Which of the following would be the BEST to use to find vulnerabilities on this server?
A. OpenVAS
B. Nikto
C. SQLmap
D. Nessus
Correct Answer: C
Reference: https://phoenixnap.com/blog/best-penetration-testing-tools
NEW QUESTION 12:
A security company has been contracted to perform a scoped insider-threat assessment to try to gain access to the human resources server that houses PII and salary data. The penetration testers have been given an internal network starting position.
Which of the following actions, if performed, would be ethical within the scope of the assessment?
A. Exploiting a configuration weakness in the SQL database
B. Intercepting outbound TLS traffic
C. Gaining access to hosts by injecting malware into the enterprise-wide update server
D. Leveraging a vulnerability on the internal CA to issue fraudulent client certificates
E. Establishing and maintaining persistence on the domain controller
Correct Answer: B
NEW QUESTION 13:
A company recruited a penetration tester to configure wireless IDS over the network. Which of the following tools would BEST test the effectiveness of the wireless IDS solutions?
A. Aircrack-ng
B. Wireshark
C. Wifite
D. Kismet
Correct Answer: A
Reference: https://purplesec.us/perform-wireless-penetration-test/
…
Download the CompTIA PT0-002 PDF 2022:
https://drive.google.com/file/d/17L47_KDIP0cQJapPpfYFN5yjBJBkT3Wg/
You can use these to improve yourself, but the free CompTIA PT0-002 Dumps exam questions will only help you warm up, I still recommend using the latest updated CompTIA PT0-002 Dumps https://www.leads4pass.com/pt0-002.html Helping you complete your CompTIA PT0-002 PenTest+ exam mission.
More IT certification blogs: [Amazon]awsexamdumps.com, [Oracle]oraclefreedumps.com, [CompTIA]CompTIAfreedumps.com, [Microsoft]examdumpsbase.com, [Citrix]citrixexamdumps.com
[CompTIA]comptiafreedumps.com, [VMware]vmwarefreedumps.com, [IBM]ibmexamdumps.com, [HP]hpexamdumps.com, [NetApp]netappexamdumps.com, [Juniper]juniperexamdumps.com
[Fortinet]fortinetexamdumps.com
