Lead4Pass has updated Cisco 350-801 dumps issues! The latest 350-801 exam questions can help you pass the exam! All questions are corrected
to ensure authenticity and effectiveness! Download the Lead4Pass 350-801 VCE dumps or PDF dumps: https://www.leads4pass.com/350-801.html (Total Questions: 347 Q&A)
Cisco 350-801 Practice testing questions from Youtbe
Braindump4it Exam Table of Contents:
- Latest Cisco 350-801 google drive
- Effective Cisco 350-801 Practice testing questions
- Lead4Pass Year-round Discount Code
- What are the advantages of Lead4pass?
Latest Cisco 350-801 google drive
[Latest PDF] Free Cisco 350-801 pdf dumps download from Google Drive: https://drive.google.com/file/d/1cIN4rk2SC3iQBAoqjJIVabGV8pyOu_wN/
[Updated 2022] https://drive.google.com/file/d/1Ri6UVCFsC8Qac9bchCfVEmVT3T0lJMzg/
[Updated 2022] Latest Cisco 350-801 dumps exam questions Free sharing
Question 1:
What is the element of Cisco Collaboration infrastructure that allows Jabber clients outside of the network to register in Cisco Unified Communications Manager and use its resources?
A. Cisco IM and Presence node
B. Cisco Unified Border Element
C. Cisco Expressway
D. Cisco Prime Collaboration Provisioning server
Correct Answer: C
Question 2:
A Cisco Unity Connection administrator must set a voice mailbox so that it can be accessed from a secondary device. Which configuration on the voice mailbox makes this change?
A. Attempt Forward routing rule
B. Alternate Extensions
C. Alternate Names
D. Mobile User
Correct Answer: B
Question 3:
Which Cisco Unified Communications Manager configuration is required for SIP MWI integrations?
A. Select “Redirecting Diversion Header Delivery – Inbound” on the SIP trunk.
B. Enable “Accept presence subscription” on the SIP Trunk Security Profile.
C. Enable “Accept unsolicited notification” on the SIP Trunk Security Profile.
D. Select “Redirecting Diversion Header Delivery – Outbound” on the SIP trunk.
Correct Answer: C
Question 4:
An engineer troubleshoots poor voice quality on multiple calls. After looking at packet captures, the engineer notices high levels of jitter. Which two areas does the engineer check to prevent jitter? (Choose two.)
A. The network meets bandwidth requirements.
B. MTP is enabled on the SIP trunk to Cisco Unified Border Element.
C. Cisco UBE manages voice traffic, not data traffic.
D. All devices use wired connections instead of wireless connections.
E. Voice packets are classified and marked.
Correct Answer: AE
Question 5:
A customer has Cisco Unity Connections that is integrated with LDAP. As a Unity Connection administrator, you have received a request to change the first name of the VM user. Where must the change be performed?
A. Cisco Unity Connection
B. Cisco Unified Communications Manager end-user
C. Active Directory
D. Cisco IM and Presence
Correct Answer: C
[Updated 2022] Get more up-to-date Cisco 350-801 exam questions and answers
Share Cisco 350-801 exam questions for free
QUESTION 1:
A customer wants a video conference with five Cisco TelePresence IX5000 Series systems. Which media resource is necessary for the design to fully utilize the immersive functions?
A. Cisco PVDM4-128
B. software conference bridge on Cisco Unified Communications Manager
C. Cisco Webex Meetings Server
D. Cisco Meeting Server
Correct Answer: D
QUESTION 2:
Refer to the exhibit.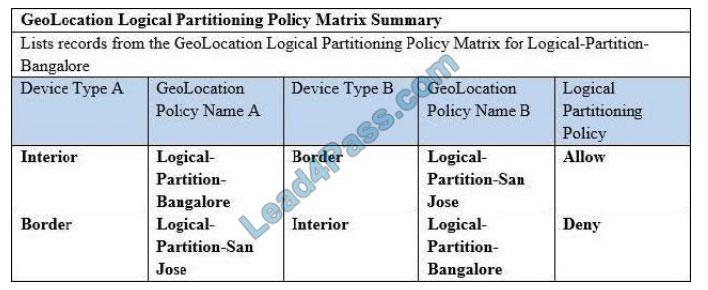
Assume that the bottom logical partition policy entry in Cisco Unified Communications Manager was provisioned last.
How is the call treated when an IP phone in the Bangalore GeoLocation places a call to an MGCP gateway with FXS ports in the San Jose GeoLocation?
A. The call is denied because the last added logical partition policy takes precedence when multiple matches exist.
B. The call is allowed because the first listed logical partition policy takes precedence when multiple matches exist.
C. The call is denied because the call flow matches neither policy entries.
D. The call is allowed because the call flow matches neither policy entries.
E. The call is allowed because only the top policy entry matches the call flow.
Correct Answer: A
QUESTION 3:
An engineer is configuring a BOT device for a Jabber user in Cisco Unified Communication Manager Which phone type must be selected?
A. third-party SIP device
B. Cisco Dual Mode for iPhone
C. Cisco Dual Mode for Android
D. Cisco Unified Client Services Framework
Correct Answer: C
QUESTION 4:
What is the major difference between the two possible Cisco IM and Presence high-availability modes?
A. Balanced mode provides user load balancing and user failover in the event of an outage. Active/standby mode provides an always-on standby node in the event of an outage, and it also provides load balancing.
B. Balanced mode provides user load balancing and user failover only for manually generated failovers. Active/standby mode provides an unconfigured standby node in the event of an outage, but it does not provide load balancing.
C. Balanced mode provides user load balancing and user failover in the event of an outage. Active/standby mode provides an always-on standby node in the event of an outage, but it does not provide load balancing.
D. Balanced mode does not provide user load balancing, but it provides in the event of an outage. Active/standby mode provides an always-on standby node in the event of an outage, but it does not provide load balancing.
Correct Answer: C
QUESTION 5:
Calls are being delivered to the end-user in a globalized format. Where does an engineer configure the calling number into a localized format?
A. route pattern
B. service parameters
C. IP phone
D. gateway
Correct Answer: D
QUESTION 6:
Which statement about Cisco Unified Communications Manager and Cisco IM and Presence backups is true?
A. Backups should be scheduled during off-peak hours to avoid system performance issues.
B. Backups are saved as .tar files and encrypted using the web administrator account.
C. Backups are saved as unencrypted .tar files.
D. Backups are not needed for subscriber Cisco Unified Communications Manager and Cisco IM and Presence servers.
Correct Answer: A
QUESTION 7:
An engineer with ID012345678 must build an international dial plan in the Cisco Unified Communications Manager. Which action should be taken when building a variable-length route pattern?
A. reduce the T302 timer to less than 4 seconds
B. configure a single route pattern for international calls
C. create a second route pattern followed by the # wildcard
D. set up all international route patterns to 0.!
Correct Answer: C
QUESTION 8:
Which field of a Real-Time Transport Protocol packet allows receiving devices to detect lost packets?
A. CSRC (Contributing Source ID)
B. Timestamp
C. Sequence number
D. SSRC (Synchronization identifier)
Correct Answer: C
QUESTION 9:
Which Cisco Unified Communications Manager service parameter should be enabled to disconnect a multiparty call when the call initiator hangs up?
A. Drop Ad Hoc Conference
B. H.225 Black Setup Destination
C. Block OffNet To OffNet Transfer
D. Enterprise Feature Access Code for Conference
Correct Answer: A
QUESTION 10:
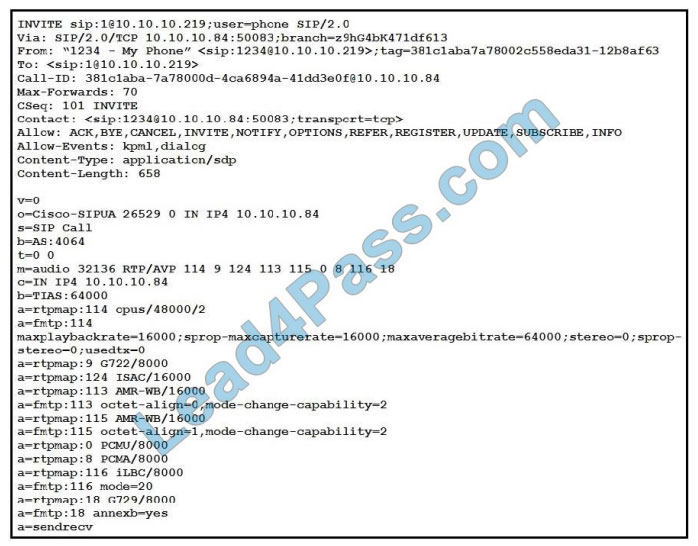
Refer to the exhibit. When a UC Administrator is troubleshooting DTMF negotiated by this SIP INVITE, which two messages should be examined next to further troubleshoot the issue? (Choose two.)
A. REGISTER
B. UPDATE
C. PACK
D. NOTIFY
E. SUBSCRIBE
Correct Answer: DE
QUESTION 11:
How can an engineer determine location-based CAC bandwidth requirements for Cisco Unified Communications Manager?
A. Set the requirements in the service parameters.
B. Add the requirements for each audio and video codec and how many calls must be supported.
C. Execute the Resource Reservation Protocol to return location-based requirements.
D. Calculate the number of calls against the license for Cisco Unified Border Element to determine calls per location.
Correct Answer: B
QUESTION 12:
Which command is used in the Cisco IOS XE TDM gateway to configure the voice T1/E1 controller to provide clocking?
A. clock source line
B. Cisco IOS XE TDM gateway T1/E1 controller cannot provide clocking.
C. clocking source internal
D. clocking source network
Correct Answer: D
QUESTION 13:
Refer to the exhibit.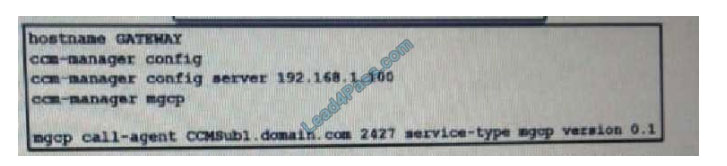
An engineer verifies the configuration of an MGCP gateway. The commands are already configured. Which command is necessary to enable MGCP?
A. Device(config)# mgcp enable
B. Device(config)# ccm-manager enable
C. Device (config) # com-manager active
D. Device (config)# mgcp
Correct Answer: D
Latest Lead4Pass Cisco dumps Discount Code 2020

About The Lead4Pass Dumps Advantage
Lead4Pass has 7 years of exam experience! A number of professional Cisco exam experts! Update exam questions throughout the year! The most complete exam questions and answers! The safest buying experience! The greatest free sharing of exam practice questions and answers!
Our goal is to help more people pass the Cisco exam! Exams are a part of life, but they are important!
In the study, you need to sum up the study! Trust Lead4Pass to help you pass the exam 100%!
Summarize:
This blog shares the latest Cisco 350-801 exam dumps, and 350-801 exam questions and answers! 350-801 pdf, 350-801 exam video!
You can also practice the test online! Lead4pass is the industry leader!
Select Lead4Pass 350-801 exams Pass Cisco 350-801 exams “Implementing and Operating Cisco Collaboration Core Technologies (CLCOR)”. Help you successfully pass the 350-801 exam.
ps.
Get Cisco Full Series Exam Dumps: https://www.vcecert.com/?s=Cisco (Updated daily)
The latest update Lead4pass 350-801 exam dumps: https://www.leads4pass.com/350-801.html (Total Questions: 347 Q&A)
[Q1-Q12 PDF] Free Cisco 350-801 pdf dumps download from Google Drive: https://drive.google.com/file/d/1cIN4rk2SC3iQBAoqjJIVabGV8pyOu_wN/
[Updated 2022] https://drive.google.com/file/d/1Ri6UVCFsC8Qac9bchCfVEmVT3T0lJMzg/