The newly updated Cisco 300-920 dumps contain 60 exam questions and answers that candidates can study using the 300-920 dumps PDF and 300-920 dumps VCE to help you successfully pass the 300-920 DEVWBX exam.
You are welcome to download the latest Cisco 300-920 dumps: https://www.leads4pass.com/300-920.html, Lead4Pass 300-920 dumps serve all candidates taking the 300-920 DEVWBX exam and guarantee you 100% Successfully passed the 300-920 DEVWBX exam.
Download the Cisco 300-920 PDF for free sharing online:
https://drive.google.com/file/d/1qSUFaHY2T85dweGiJgUn5RVDy8RRukVE/
Share the latest Cisco 300-920 dumps exam questions and answers for free
New Question 1:
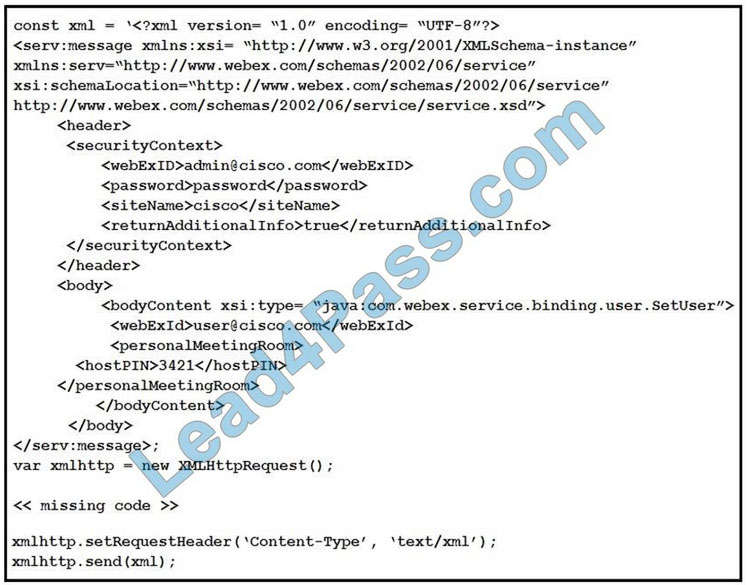
Refer to the exhibit. A developer must construct an HTTP Request to use the XML API to set a Personal Meeting Room PIN for a given user.
Which code completes the code to create the request?
A. xmlhttp.open(“GET”, “https://cisco.webex.com/WBXService/XMLService”);
B. xmlhttp.open(“PATCH”, “https://cisco.webex.com/WBXService/XMLService”);
C. xmlhttp.open(“PUT”, “https://cisco.webex.com/WBXService/XMLService”);
D. xmlhttp.open(“POST”, “https://cisco.webex.com/WBXService/XMLService”);
Correct Answer: D
The post method can be used for HTTP request that sets up a personal metting room PIN for a user.
New Question 2:
Which two items are needed to give a Webex user the ability to archive all Webex Teams messages for an organization? (Choose two.)
A. Give the user “Read-only administrator privileges” in the Webex Control Hub.
B. Create an Integration app with all “spark_compliance” read scopes enabled.
C. Use the Webex Meetings XML API “SetUser” to update the user\’s “” value to “TRUE”.
D. Configure the user as a “Compliance Officer” in the Webex Control Hub.
E. Create a Bot app with all “webex_compliance” read scopes enabled.
Correct Answer: AD
New Question 3:
What happens if a meeting is in progress when a DelMeeting request is sent in the Webex Meetings XML API?
A. The meeting host is notified and prompted to allow the meeting to be deleted.
B. The DelMeeting request drops all call-in users and deletes the meeting.
C. The DelMeeting request waits until the meeting is completed and then deletes the meeting.
D. The DelMeeting request results in an error.
Correct Answer: A
New Question 4:
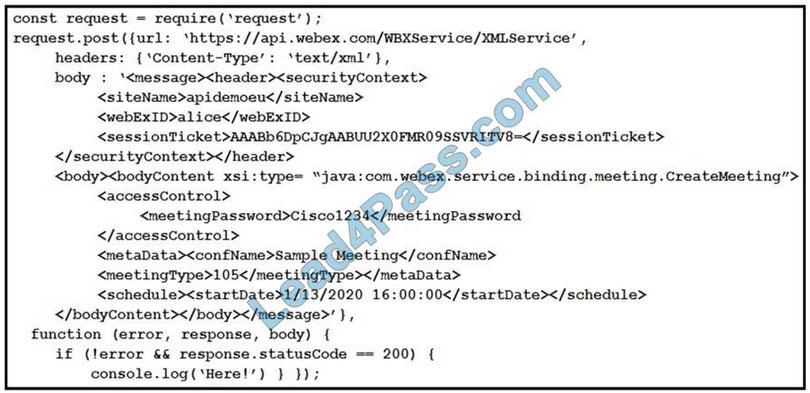
Refer to the exhibit. The Node.js script shown uses the Webex Meetings XML API to print “Here!” to the console.
Which statement is a correct observation about the results of the script?
A. The was not complex enough.
B. The credential was expired.
C. The WebexMeetings XML API service processed the request.
D. The meeting was created successfully.
Correct Answer: C
The password, although not that good, has capital letters and numbers. Therefore, it is okay. SessionTicket credential is not expired because the error function doesn\’t checks that. We are not sure if the meeting was created successfully however, there is no wrong in the code, therefore, WebEx meetings XML API service has processed the request.
New Question 5:
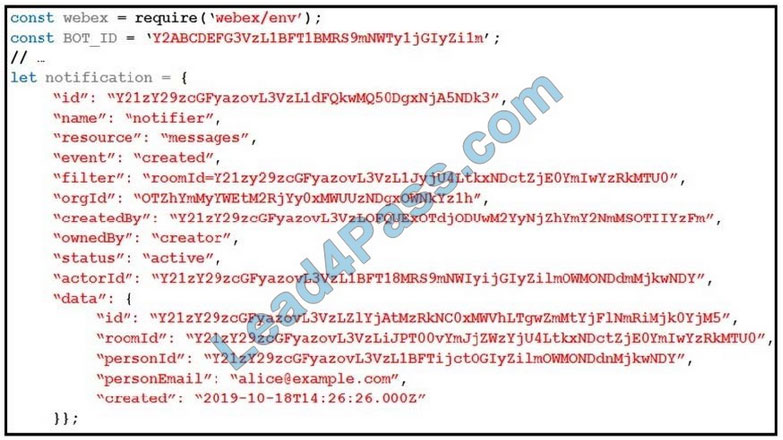
Refer to the exhibit. A webhook has been created so that an application is notified when users mention a bot in a Webex Teams space. The exhibit shows an example of a notification received by the application. Which code snippet correctly processes the JSON payload using the Webex Node.js SDK in order to print out messages that mention the bot?
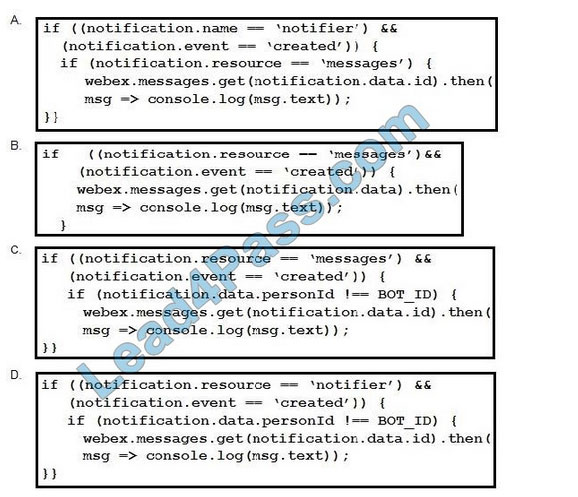
A. Option A
B. Option B
C. Option C
D. Option D
Correct Answer: B
New Question 6:
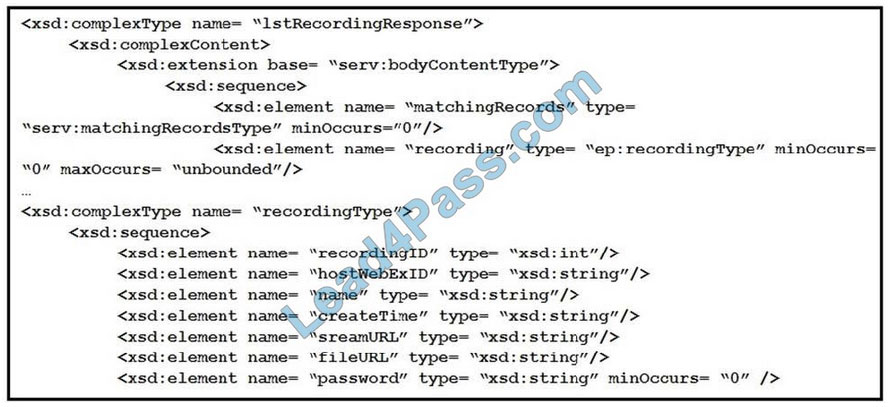
Refer to the exhibit. A snippet from the XSD schema of the Webex Meeting XML API LstRecordingResponse\' element is listed in the exhibit. Assuming that a variable namedresp\’ exists that contains the XML response from a successful `LstRecording\’ request, which code snippet correctly generates a simple report that lists meeting names and recording file download links?
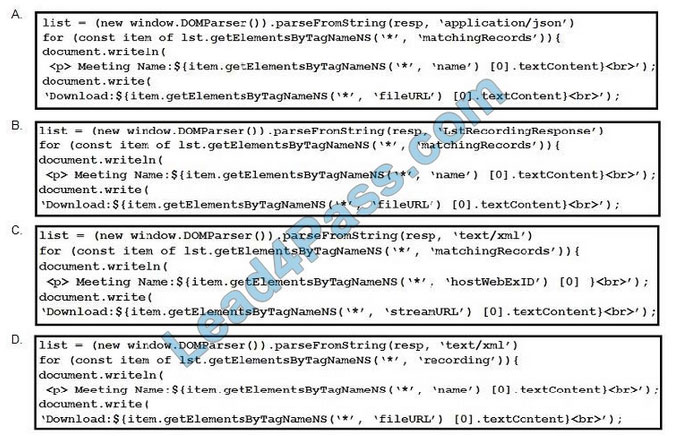
A. Option A
B. Option B
C. Option C
D. Option D
Correct Answer: A
New Question 7:
Which xAPI access mechanism requires separate connections for commands and notifications?
A. Serial
B. WebSocket
C. HTTP/HTTPS
D. SSH
Correct Answer: D
New Question 8:
Which two capabilities are currently supported by the Webex Meetings XML API? (Choose two.)
A. Request a recording link for playback.
B. Send a text message to the meeting host.
C. Request permissions to schedule on someone else\’s behalf.
D. Schedule a new meeting.
E. Send a problem report.
Correct Answer: CD
New Question 9:
Which two statements about Webex Teams refresh tokens are true? (Choose two.)
A. The refresh token is useless without the client ID and client secret.
B. An attacker can use the refresh token to send messages on behalf of the user.
C. The refresh token is used to generate a new access token.
D. A new refresh token cannot be granted until the client ID is invalidated.
E. The refresh token does not expire.
Correct Answer: BC
New Question 10:
Which element is needed to build a Web application that authenticates Webex users and can post messages under the user\’s identity?
A. OAuth integration configured with the `messages_write\’ scope
B. bot access token
C. Guest Issuer application
D. self-signed certificate that is created from a public authority
Correct Answer: A
New Question 11:
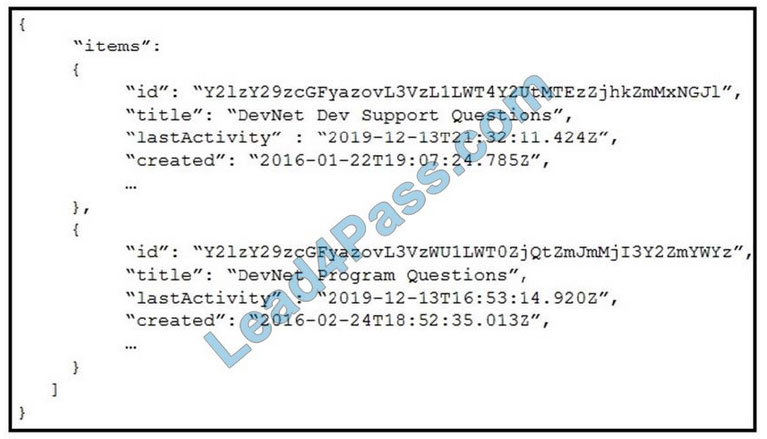
Refer to the exhibit. Which Webex Teams REST API request has generated the response body in the exhibit?
A. GET/v1/rooms?sortBy=lastactivity
B. GET/v1/rooms?sortBy=created
C. GET/v1/rooms?max=1
D. GET/v1/spaces?orderBy=lastActivity
Correct Answer: C
New Question 12:
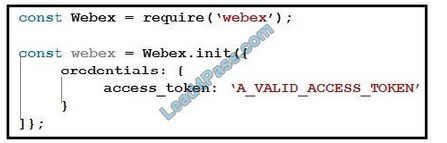
Refer to the exhibit. When using the Webex Browser SDK to create calls and share screens, which two statements are valid given a `webex\’ object such as displayed in the exhibit? (Choose two.)
A. After a meeting is joined, it cannot be left programmatically until the host ends the meeting.
B. The webex meetings.register() function must be invoked before attempting to join any meeting.
C. The joinMeeting() function throws an error of type `media stopped\’ if a media stream is stopped.
D. Given a Webex meeting number the webex meetings join() function can be used to join the meeting.
E. The mediaSettings for a joined meeting accepts boolean attributes to send and receive audio, video, and screen share.
Correct Answer: AB
New Question 13:
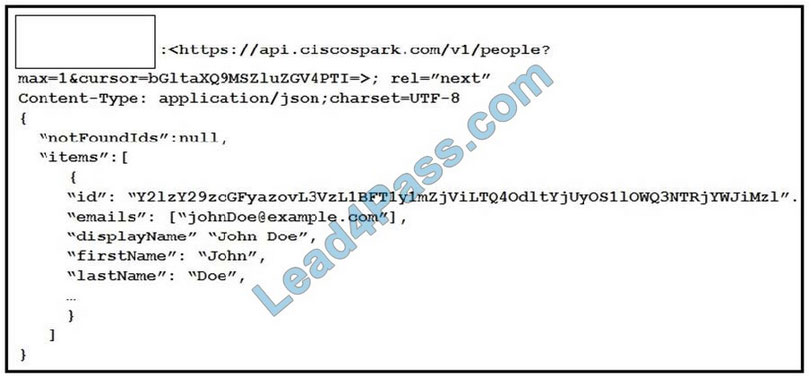
Refer to the exhibit. A Webex Teams REST API response is shown with the HTTP Header missing.
Which HTTP header is expected in this response?
A. Push
B. Link
C. Patch
D. Put
Correct Answer: B
New Question 14:
A company wants to adopt Webex Teams as a messaging platform and use REST APIs to automate the creation of teams and rooms.
Which sequence of REST API requests is needed to create and populate a new Webex team and create a populated Webex room for the team?
A. POST /teams, POST /memberships, POST /rooms
B. POST /teams, POST /people, POST /rooms
C. POST /teams, POST /team/memberships, POST /rooms
D. POST /teams, POST /team/memberships, POST /rooms, POST /memberships
Correct Answer: B
Question 15:
Which Webex Teams webhook resource type indicates that a user interacted with a card?
A. buttonActions
B. attachmentActions
C. webhookCardActions
D. cardActions
Correct Answer: B
…
Download the Cisco 300-920 PDF for free sharing online:
https://drive.google.com/file/d/1qSUFaHY2T85dweGiJgUn5RVDy8RRukVE/
The above is only a part of Cisco 300-920 dumps exam questions and answers, you can use the above exam questions and answers to improve yourself, not only that, we welcome you to download the latest
Cisco 300-920 dumps exam questions: https://www.leads4pass.com/300-920.html (Total Questions: 60 Q&A), help you truly pass the 300-920 DEVWBX exam.
More IT certification blogs: [Amazon]awsexamdumps.com, [Oracle]oraclefreedumps.com, [Cisco]ciscofreedumps.com, [Microsoft]examdumpsbase.com, [Citrix]citrixexamdumps.com
[CompTIA]comptiafreedumps.com, [VMware]vmwarefreedumps.com, [IBM]ibmexamdumps.com, [HP]hpexamdumps.com, [NetApp]netappexamdumps.com, [Juniper]juniperexamdumps.com
[Fortinet]fortinetexamdumps.com